Connect Microsoft 365 to Anzenna
Integrate Anzenna with Microsoft 365 to monitor users, devices, applications, and activity. Optionally enable password reset, app uninstall, activity monitoring, and Defender Live Response capabilities.
Prerequisites
Microsoft 365 Global Administrator or equivalent access
- Access to the Anzenna platform
PowerShell (for optional remediation scripts)
Step-by-Step Instructions
Part 1: Connect Microsoft 365
Go to app.anzenna.ai and click Sign in with Microsoft.
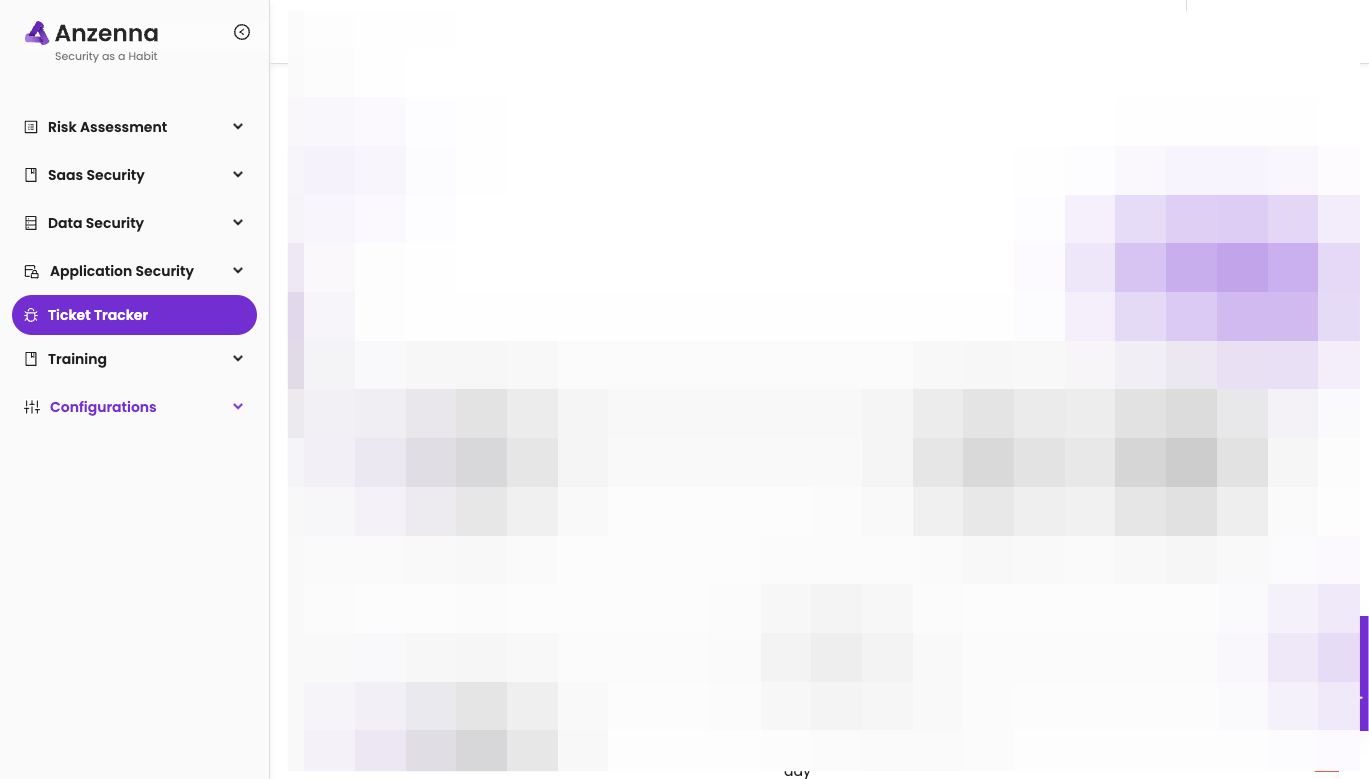
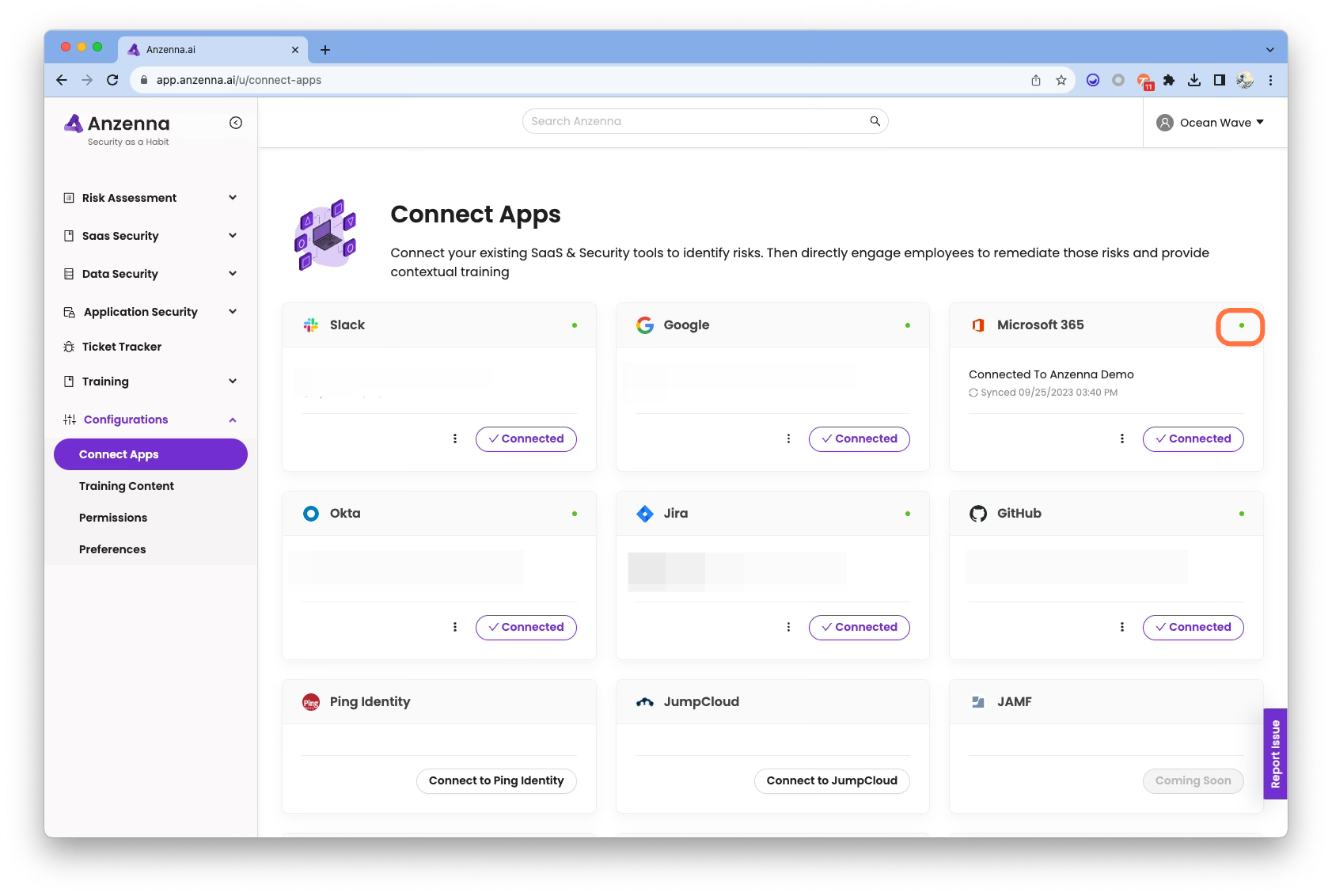
Click on Configurations.
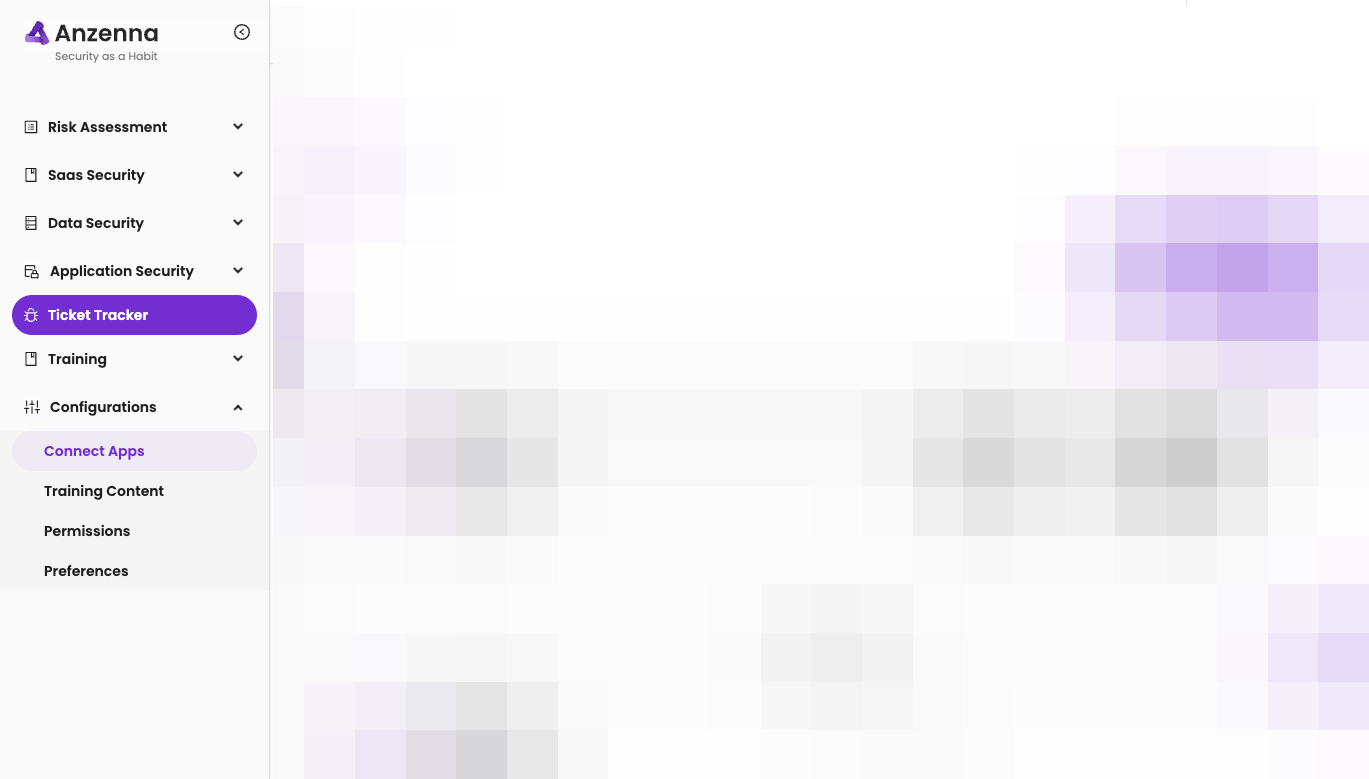
Click on Connect Apps.
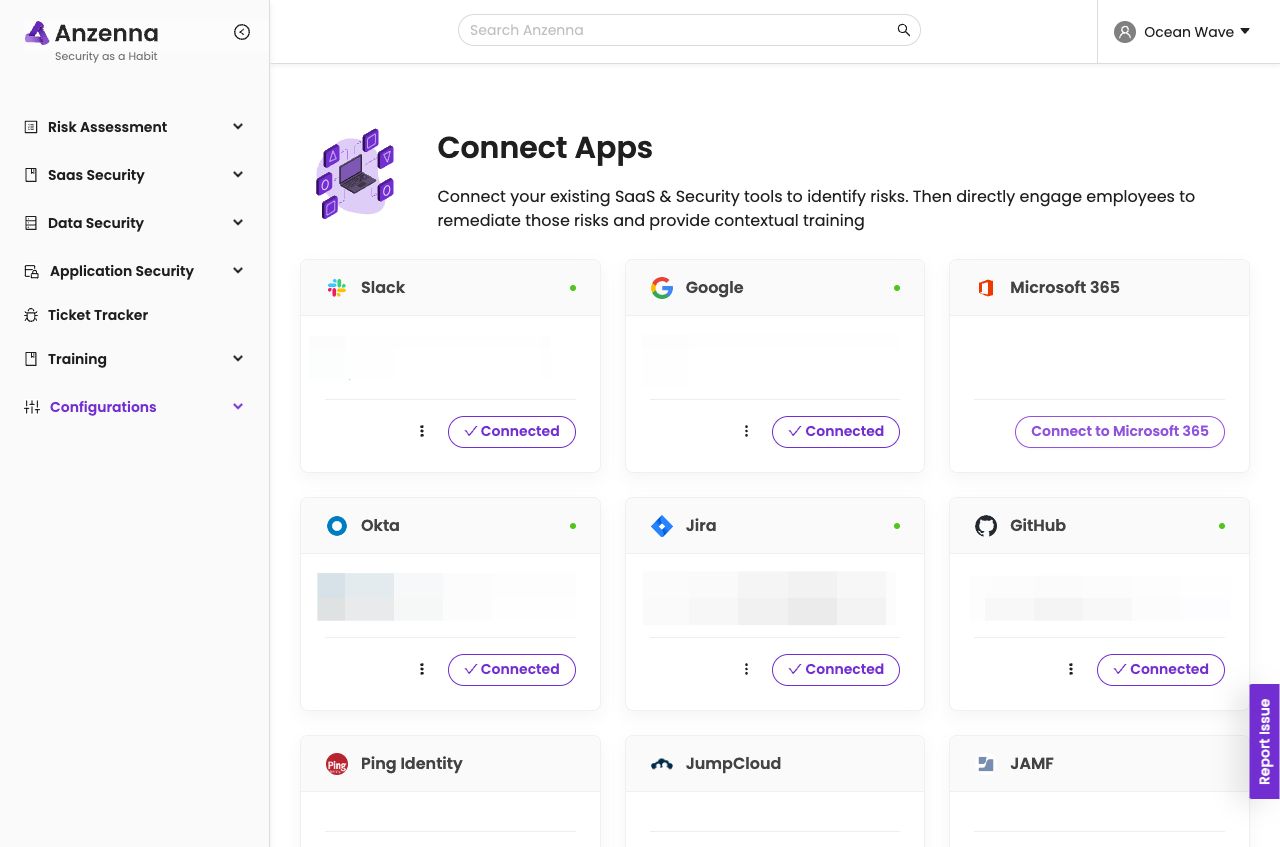
Click on Connect to Microsoft 365.
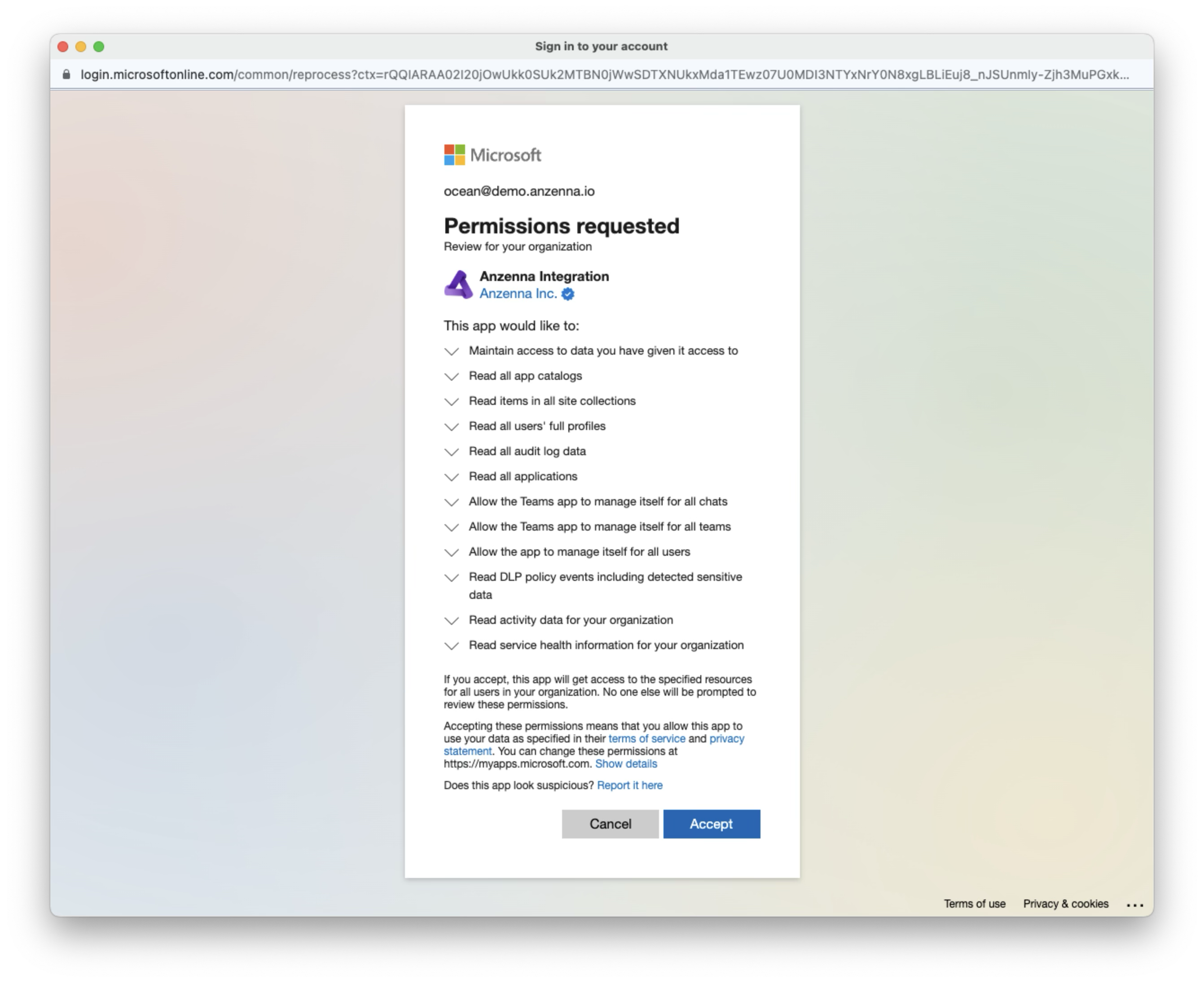
Sign in with your Microsoft account, then Review and Accept the requested permissions.
Your Microsoft account is now connected to Anzenna.
Core setup complete! Anzenna is now connected to Microsoft 365. The sections below cover optional remediation and monitoring features.
Part 2: [Optional] Allow Password Reset for Compromised Users
This grants Anzenna permission to reset passwords of potentially compromised (non-admin) users. Note: this does not grant permission to reset administrator passwords.
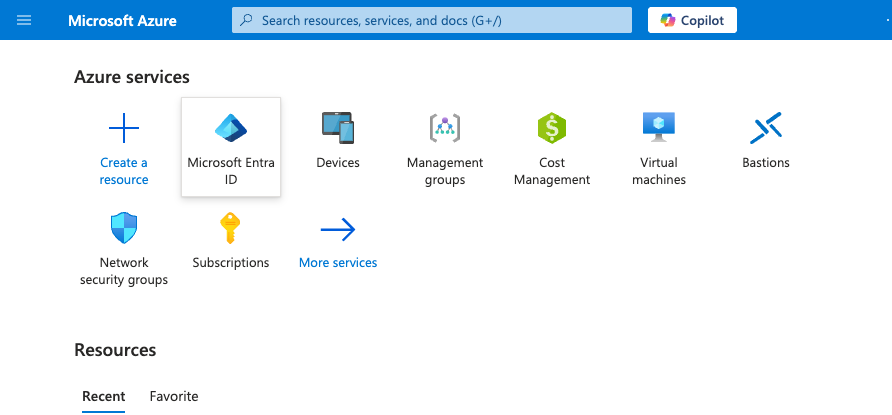
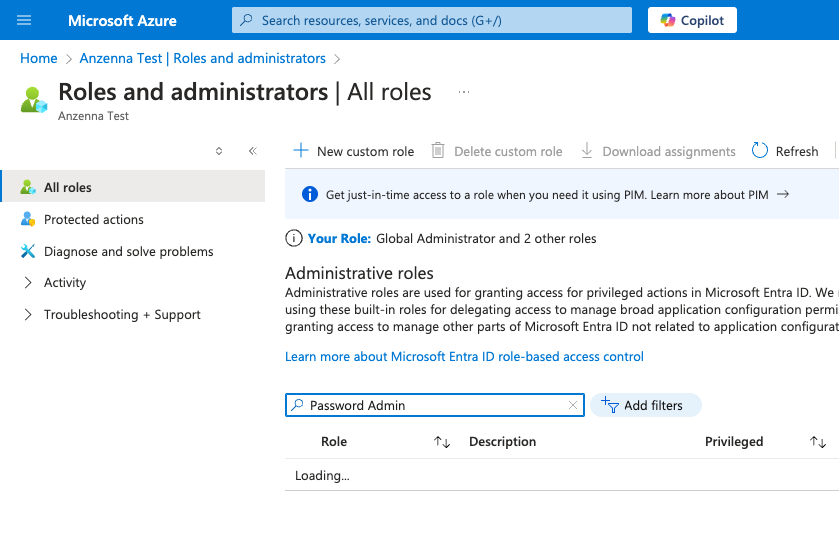
Go to portal.azure.com and click on Microsoft Entra ID.
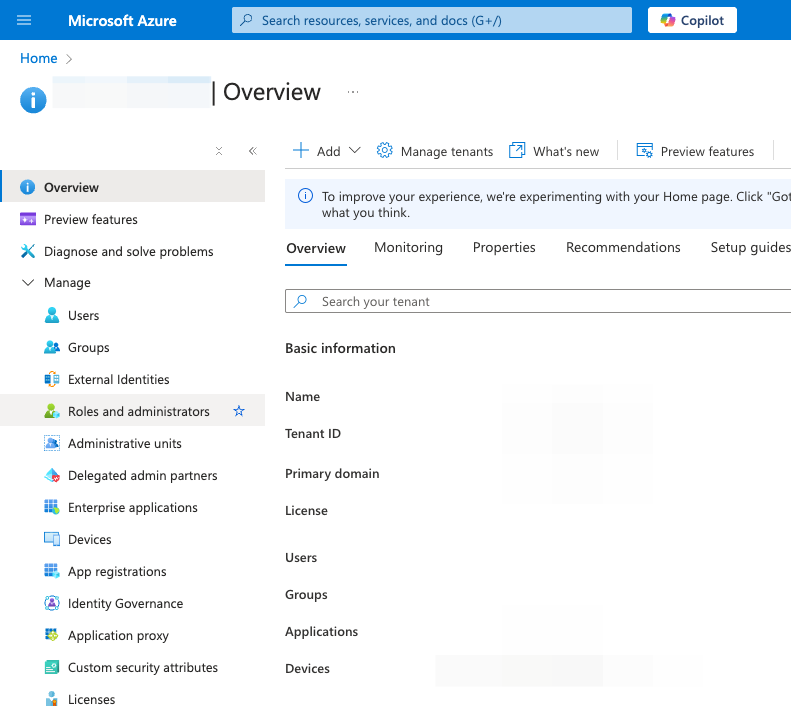
Click on Roles and administrators.
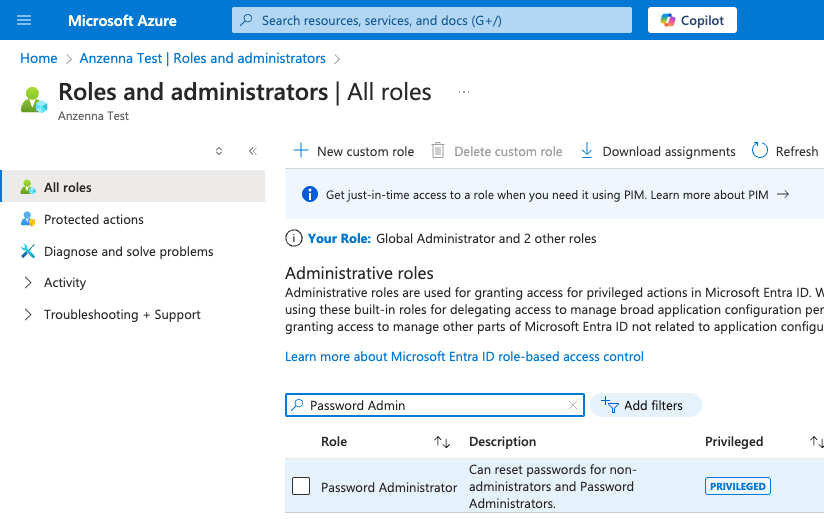
Type Password Admin in the filter box.
Click on Password Administrator.
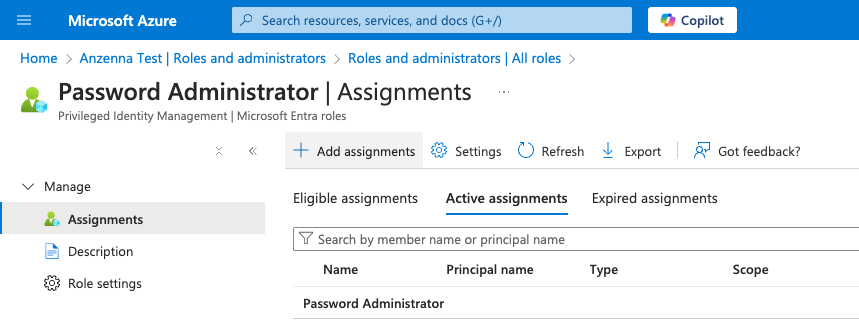
Click on Add assignments.
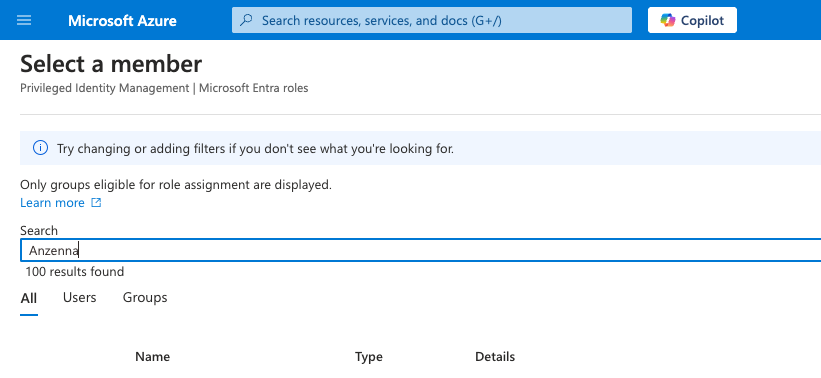
Click on No member selected.
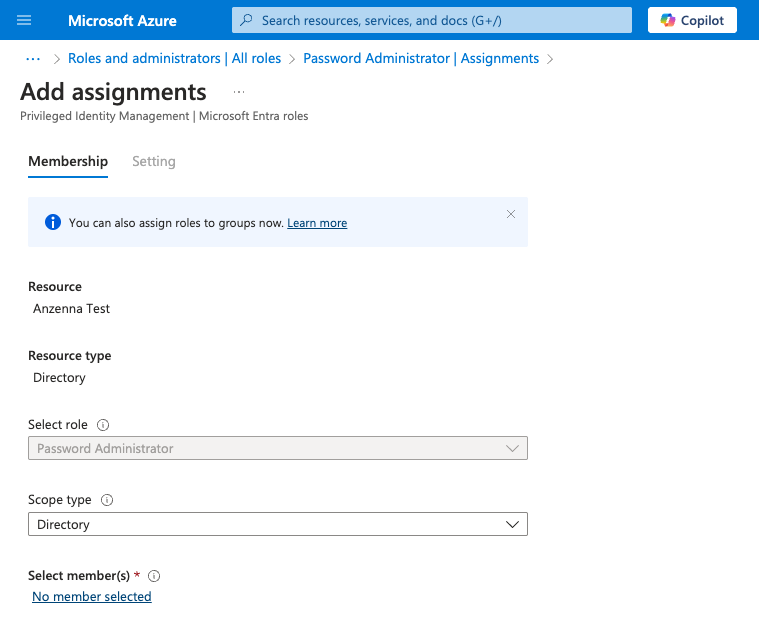
Type Anzenna to search.
Click on Enterprise applications.
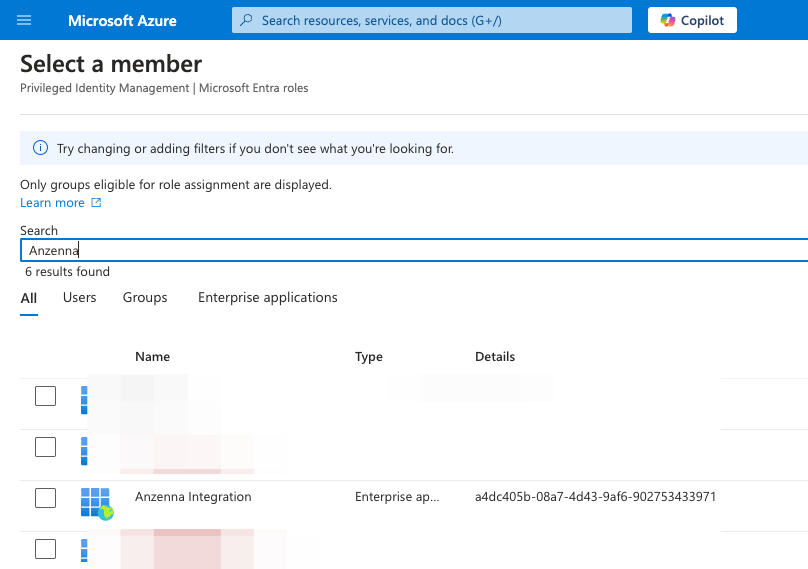
- Click on the Anzenna row to select it.
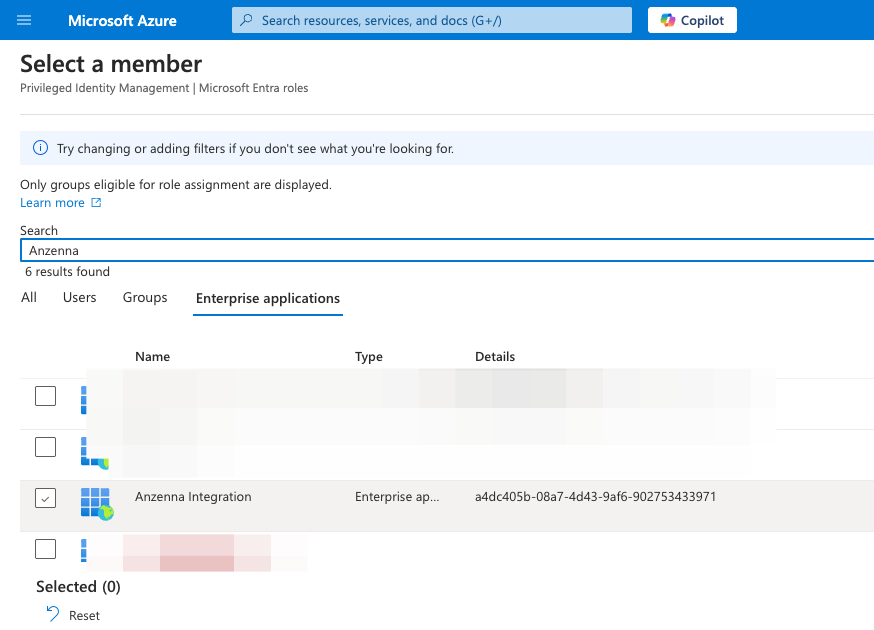
Click Select.
Click Next.
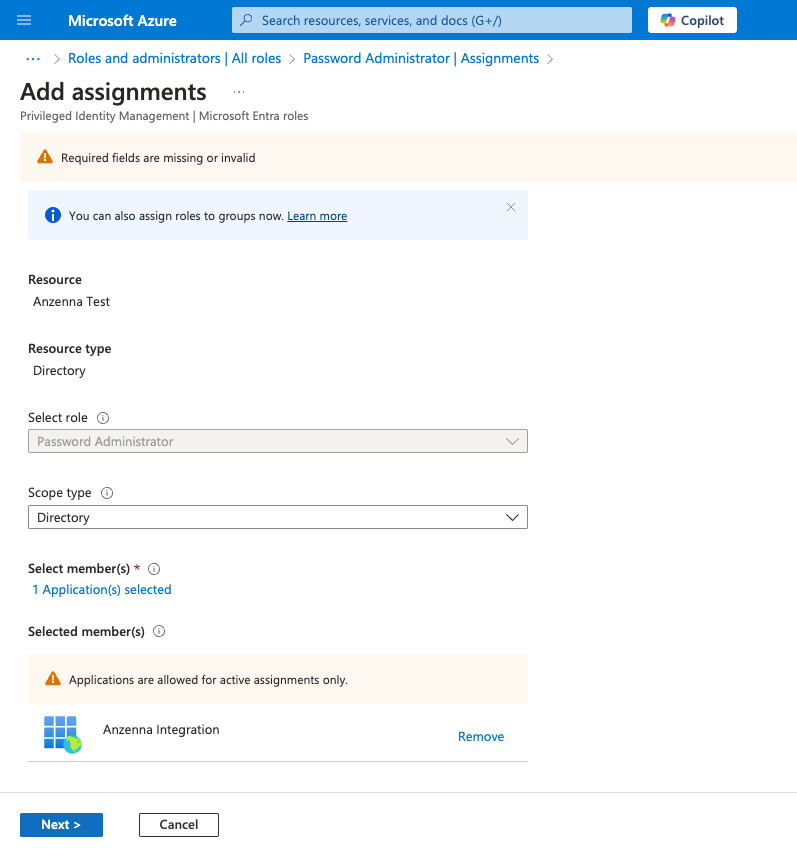
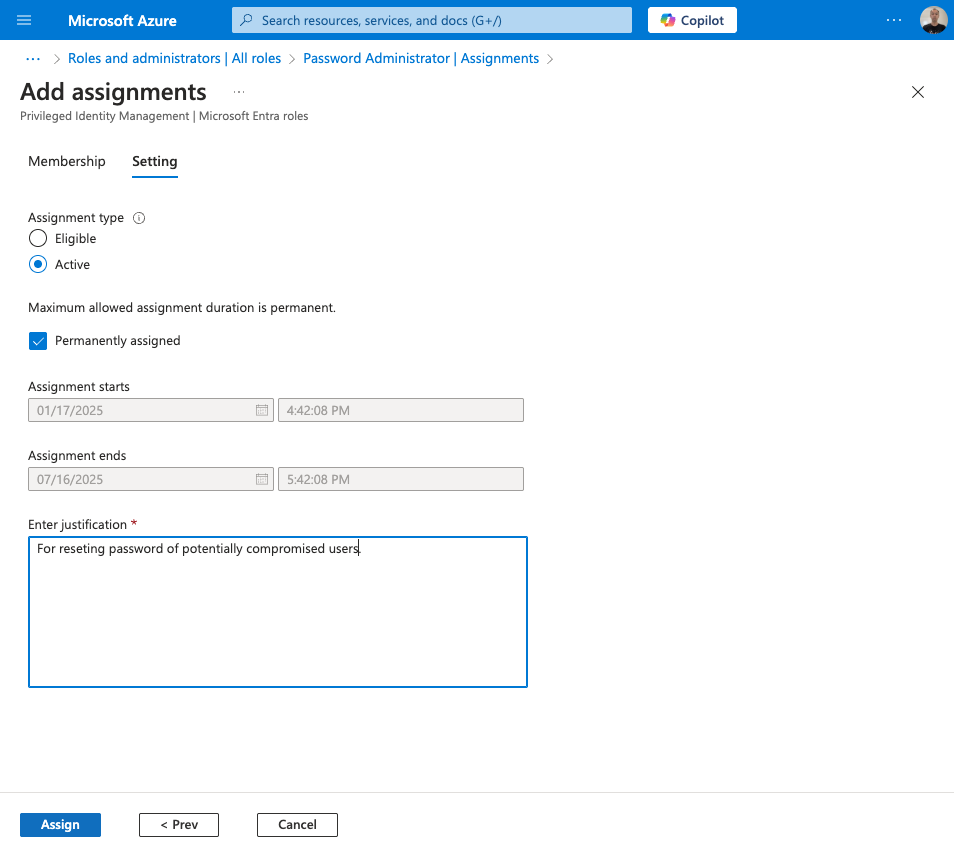
Enter a justification such as "For resetting password of potentially compromised users." then click Assign.

Next, run the following PowerShell scripts to grant Anzenna the necessary Graph API write permissions. If you do not have PowerShell, download it from
Microsoft's PowerShell page
.
Step 1: Install the Microsoft Graph module (run once):
Install-Module Microsoft.Graph
Step 2: Grant Anzenna write permissions for password reset:
$ErrorActionPreference = "Stop"
$GraphAppID = "00000003-0000-0000-c000-000000000000"
$AnzennaAppID = "a4dc405b-08a7-4d43-9af6-902753433971"
$InteractivePermissions = @("Application.Read.All", "AppRoleAssignment.ReadWrite.All")
$AnzennaPermissions = @("User.ReadWrite.All", "Group.ReadWrite.All")
Write-Host "Connecting to Microsoft Graph"
Write-Host "***************************************************"
Write-Host "NOTE: Do not consent on behalf of your organization"
Write-Host "***************************************************"
Connect-MgGraph -Scopes $InteractivePermissions -NoWelcome
$msgraph = Get-MgServicePrincipal -Filter "AppId eq '$GraphAppID'"
$graphResourceID = $msgraph.Id
$appRoles = $msgraph.AppRoles
$anzenna = Get-MgServicePrincipal -Filter "AppId eq '$AnzennaAppID'"
$anzennaResourceID = $anzenna.Id
$roleMap = @{}
foreach ($role in $appRoles) { $roleMap[$role.Value] = $role.Id }
foreach ($permission in $AnzennaPermissions) {
$roleID = $roleMap[$permission]
$params = @{ principalId = $anzennaResourceID; resourceId = $graphResourceID; appRoleId = $roleID }
try {
New-MgServicePrincipalAppRoleAssignment -ServicePrincipalId $graphResourceID -BodyParameter $params -ErrorAction Stop > $null
Write-Host "Added $permission"
} catch {
if ($_.Exception.Message.Contains("Permission being assigned already exists on the object")) {
Write-Host "$permission has already been configured"; continue
}
Write-Error "Failed to add ${permission}: $_"; exit 1
}
}
Write-Host "Completed successfully"; exit 0
Part 3: [Optional] Allow Uninstall of Potentially Unwanted Software
This uses the same PowerShell approach as Part 2 but grants device management permissions instead.
Step 1: Install the Microsoft Graph module (run once):
Install-Module Microsoft.Graph
Step 2: Grant Anzenna write permissions for app management:
$ErrorActionPreference = "Stop"
$GraphAppID = "00000003-0000-0000-c000-000000000000"
$AnzennaAppID = "a4dc405b-08a7-4d43-9af6-902753433971"
$InteractivePermissions = @("Application.Read.All", "AppRoleAssignment.ReadWrite.All")
$AnzennaPermissions = @("DeviceManagementConfiguration.ReadWrite.All", "Group.ReadWrite.All")
Write-Host "Connecting to Microsoft Graph"
Write-Host "***************************************************"
Write-Host "NOTE: Do not consent on behalf of your organization"
Write-Host "***************************************************"
Connect-MgGraph -Scopes $InteractivePermissions -NoWelcome
$msgraph = Get-MgServicePrincipal -Filter "AppId eq '$GraphAppID'"
$graphResourceID = $msgraph.Id
$appRoles = $msgraph.AppRoles
$anzenna = Get-MgServicePrincipal -Filter "AppId eq '$AnzennaAppID'"
$anzennaResourceID = $anzenna.Id
$roleMap = @{}
foreach ($role in $appRoles) { $roleMap[$role.Value] = $role.Id }
foreach ($permission in $AnzennaPermissions) {
$roleID = $roleMap[$permission]
$params = @{ principalId = $anzennaResourceID; resourceId = $graphResourceID; appRoleId = $roleID }
try {
New-MgServicePrincipalAppRoleAssignment -ServicePrincipalId $graphResourceID -BodyParameter $params -ErrorAction Stop > $null
Write-Host "Added $permission"
} catch {
if ($_.Exception.Message.Contains("Permission being assigned already exists on the object")) {
Write-Host "$permission has already been configured"; continue
}
Write-Error "Failed to add ${permission}: $_"; exit 1
}
}
Write-Host "Completed successfully"; exit 0
Part 4: [Optional] Turn On Microsoft Office Activity Monitoring
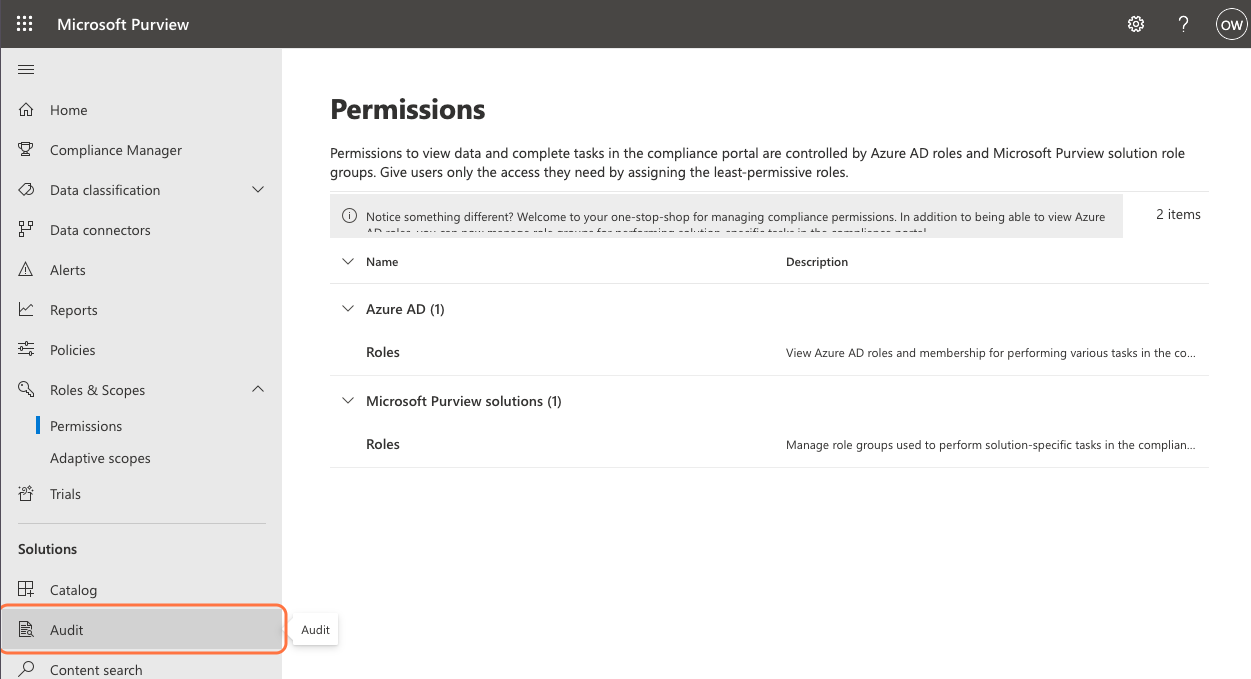
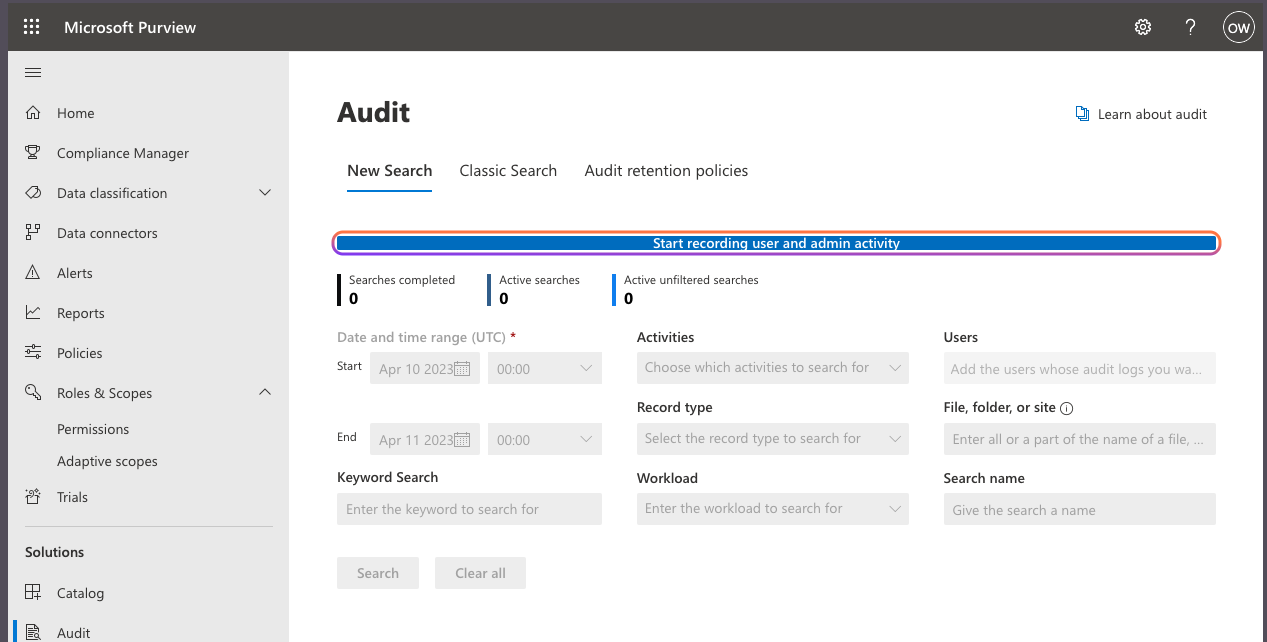
Go to purview.microsoft.com and click on Audit.
(If using the older UI, the layout will differ as shown below.)
Click on Start recording user and admin activity.
Part 5: [Optional] Allow Defender for Endpoint Live Response
Step 1: Install the Microsoft Graph module (run once):
Install-Module Microsoft.Graph
Step 2: Grant Anzenna Defender Live Response execution permissions:
$ErrorActionPreference = "Stop"
$DefenderAppID = "fc780465-2017-40d4-a0c5-307022471b92"
$AnzennaAppID = "a4dc405b-08a7-4d43-9af6-902753433971"
$InteractivePermissions = @("Application.Read.All", "AppRoleAssignment.ReadWrite.All")
$AnzennaPermissions = @("Library.Manage", "Machine.LiveResponse", "Machine.Read.All", "Machine.ReadWrite.All", "Software.Read.All")
Write-Host "Connecting to Microsoft Graph"
Write-Host "***************************************************"
Write-Host "NOTE: Do not consent on behalf of your organization"
Write-Host "***************************************************"
Connect-MgGraph -Scopes $InteractivePermissions -NoWelcome
$msgraph = Get-MgServicePrincipal -Filter "AppId eq '$DefenderAppID'"
$defenderResourceID = $msgraph.Id
$appRoles = $msgraph.AppRoles
$anzenna = Get-MgServicePrincipal -Filter "AppId eq '$AnzennaAppID'"
$anzennaResourceID = $anzenna.Id
$roleMap = @{}
foreach ($role in $appRoles) { $roleMap[$role.Value] = $role.Id }
foreach ($permission in $AnzennaPermissions) {
$roleID = $roleMap[$permission]
$params = @{ principalId = $anzennaResourceID; resourceId = $defenderResourceID; appRoleId = $roleID }
try {
New-MgServicePrincipalAppRoleAssignment -ServicePrincipalId $defenderResourceID -BodyParameter $params -ErrorAction Stop > $null
Write-Host "Added $permission"
} catch {
if ($_.Exception.Message.Contains("Permission being assigned already exists on the object")) {
Write-Host "$permission has already been configured"; continue
}
Write-Error "Failed to add ${permission}: $_"; exit 1
}
}
Write-Host "Completed successfully"; exit 0
Go to security.microsoft.com and click on System.
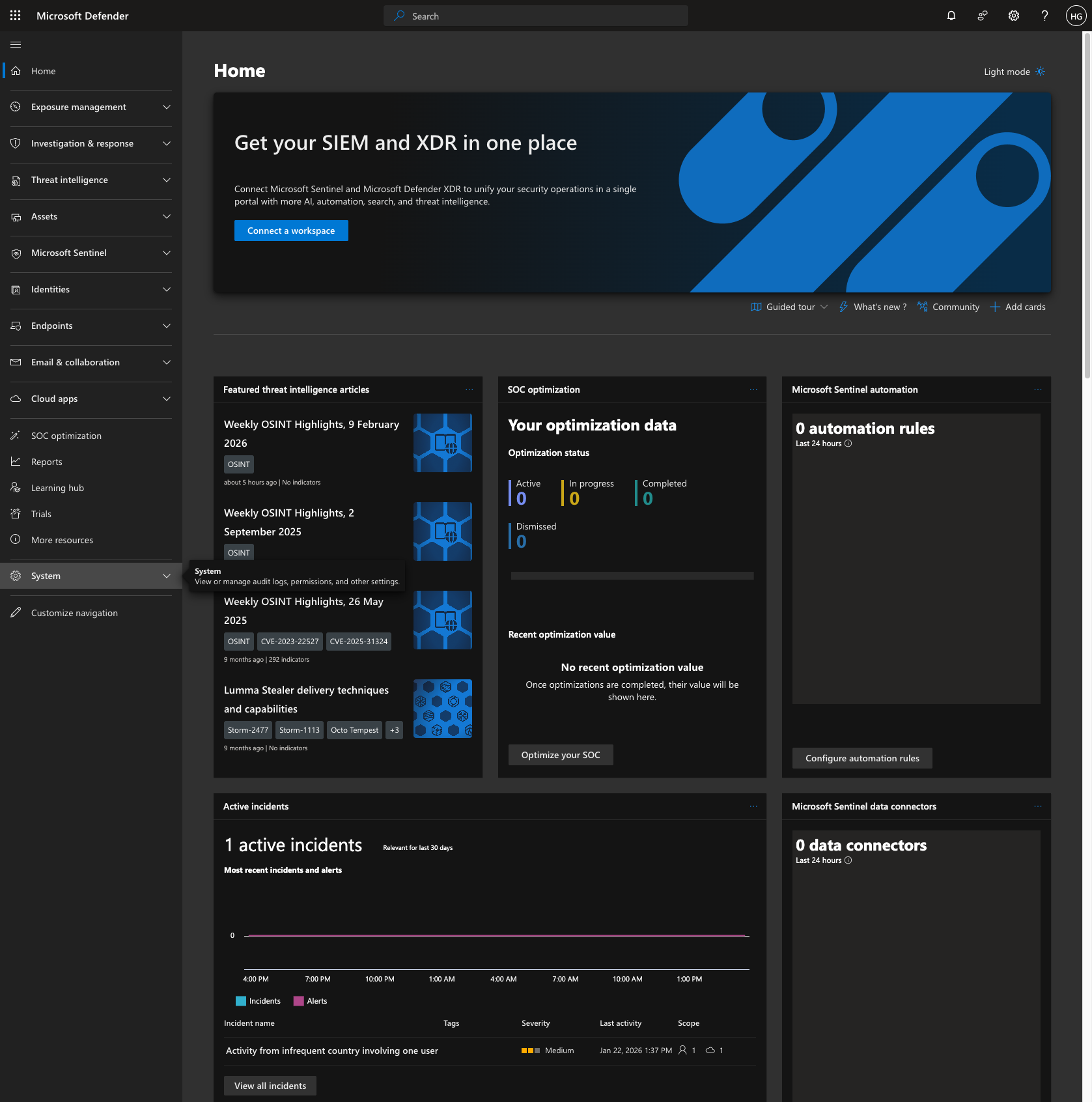
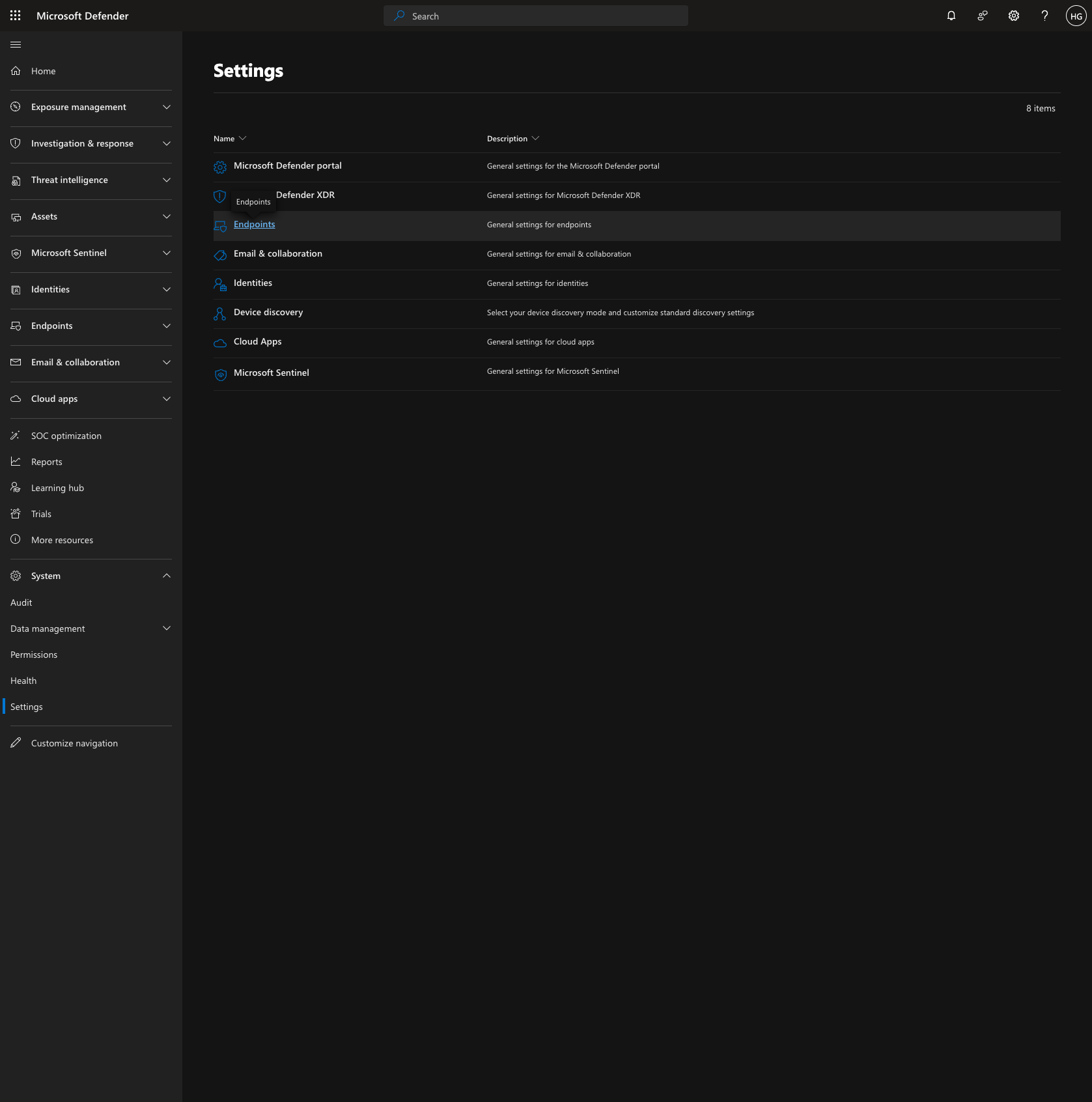
Click on Settings.

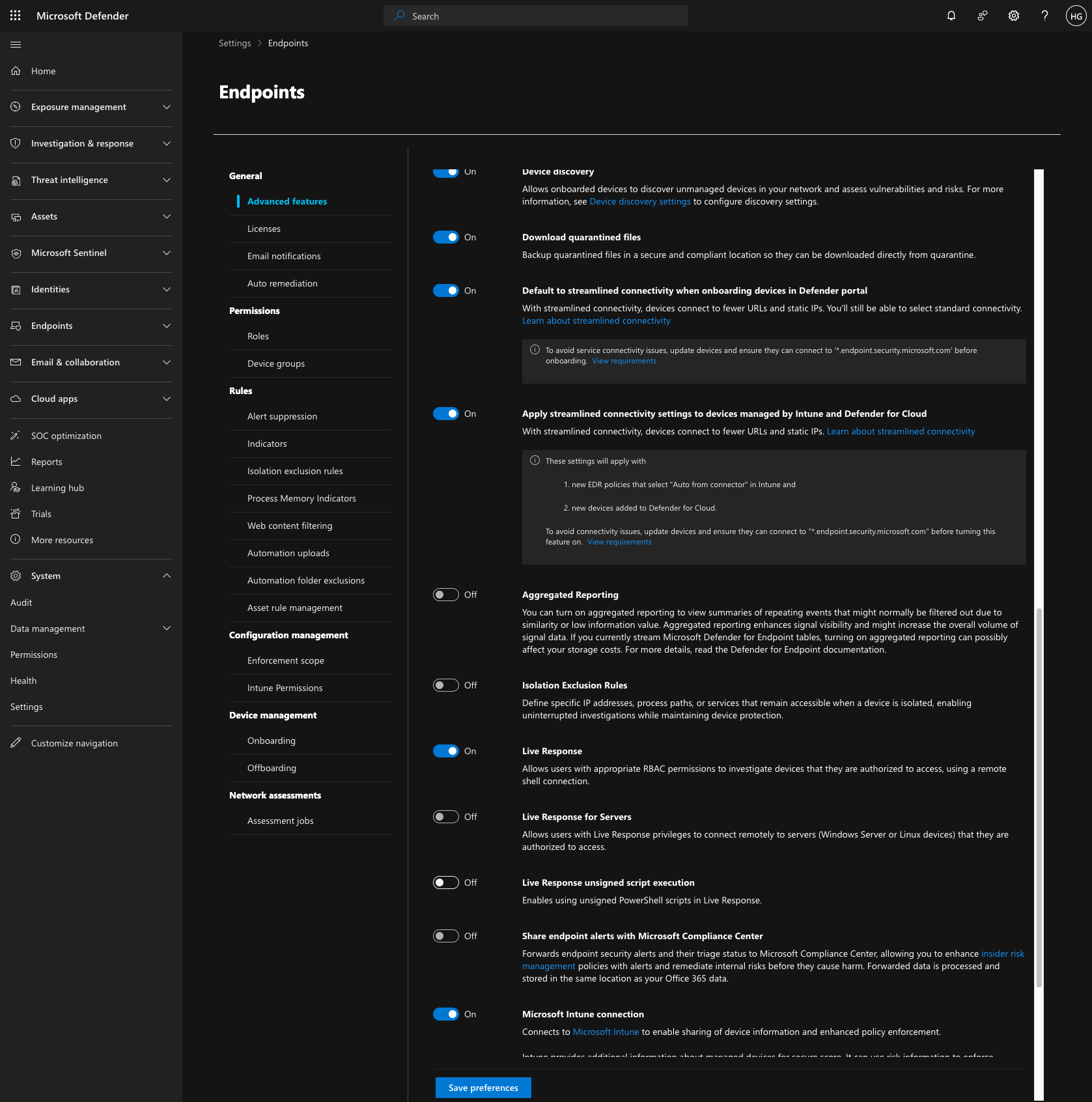
Click on Endpoints.
Click on Live Response.
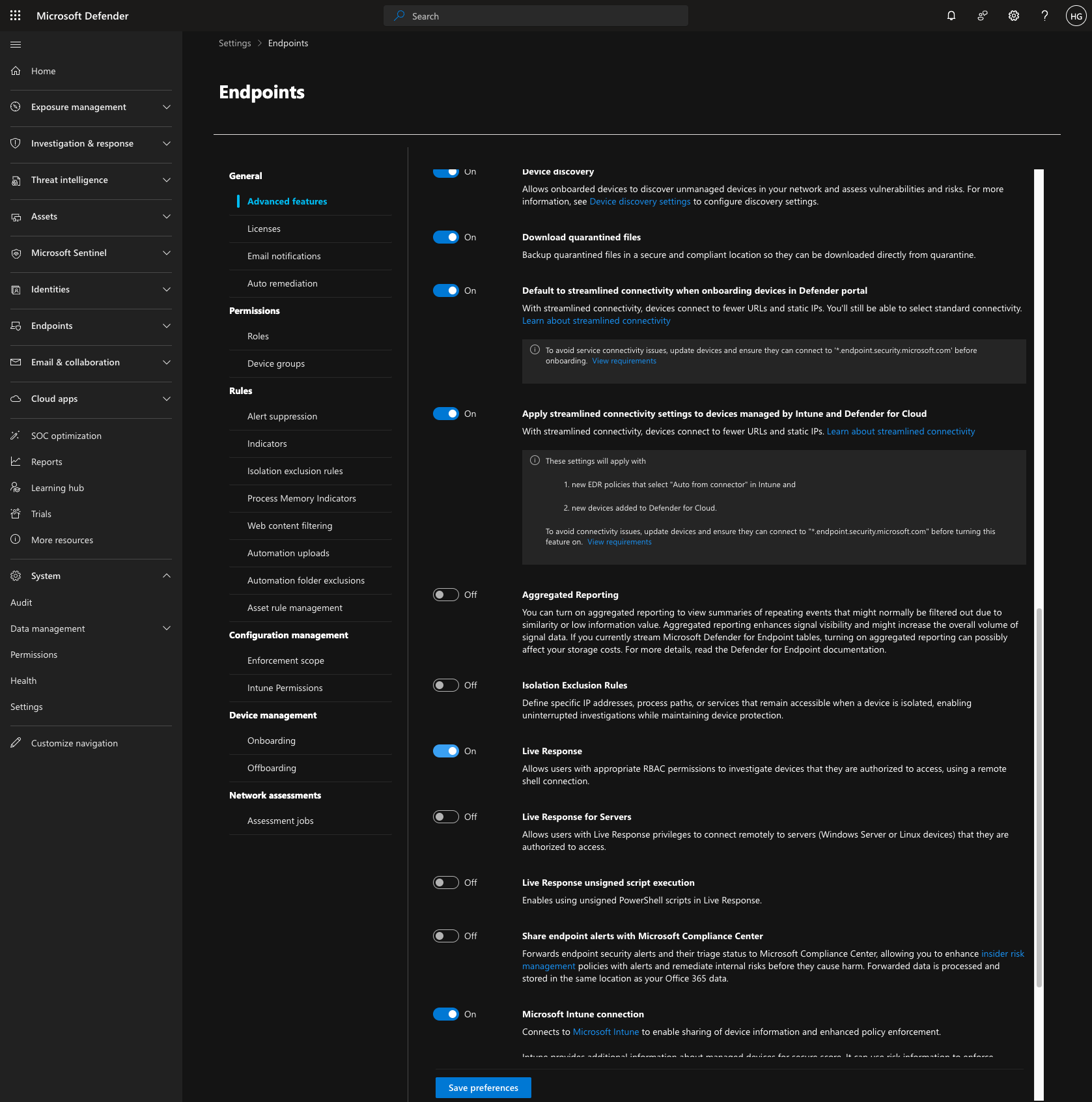
Click on Live Response unsigned script execution to enable it.
You are all set! Anzenna is now fully connected to Microsoft 365 with the capabilities you have configured.