Connect SentinelOne to Anzenna
This guide walks you through creating a service user in the SentinelOne Management Console and connecting it to Anzenna for endpoint security monitoring, threat detection, and device visibility.
Prerequisites
SentinelOne Management Console administrator access
- Access to the Anzenna platform
Step-by-Step Instructions
Part 1: Create a Service User in SentinelOne
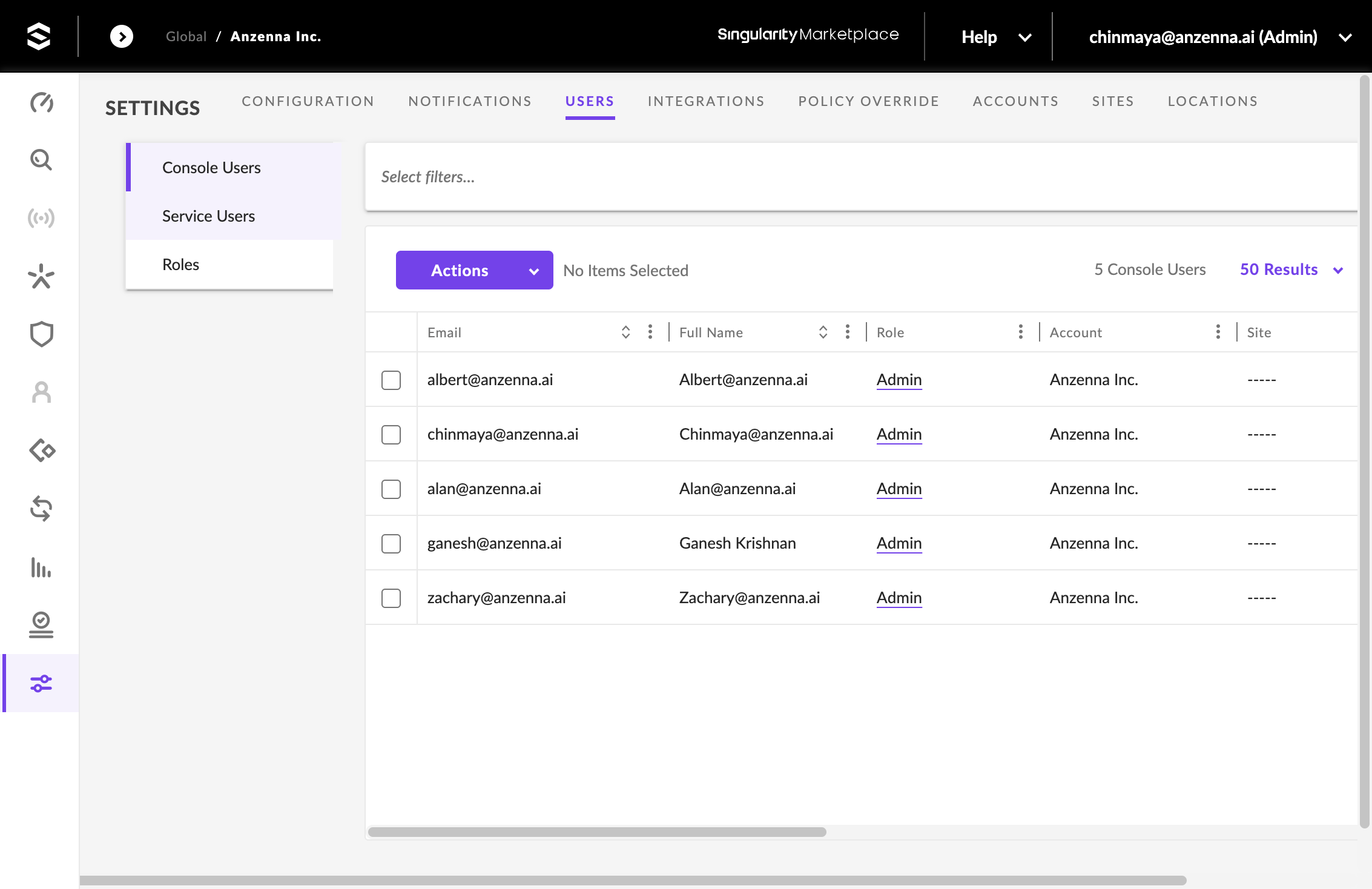
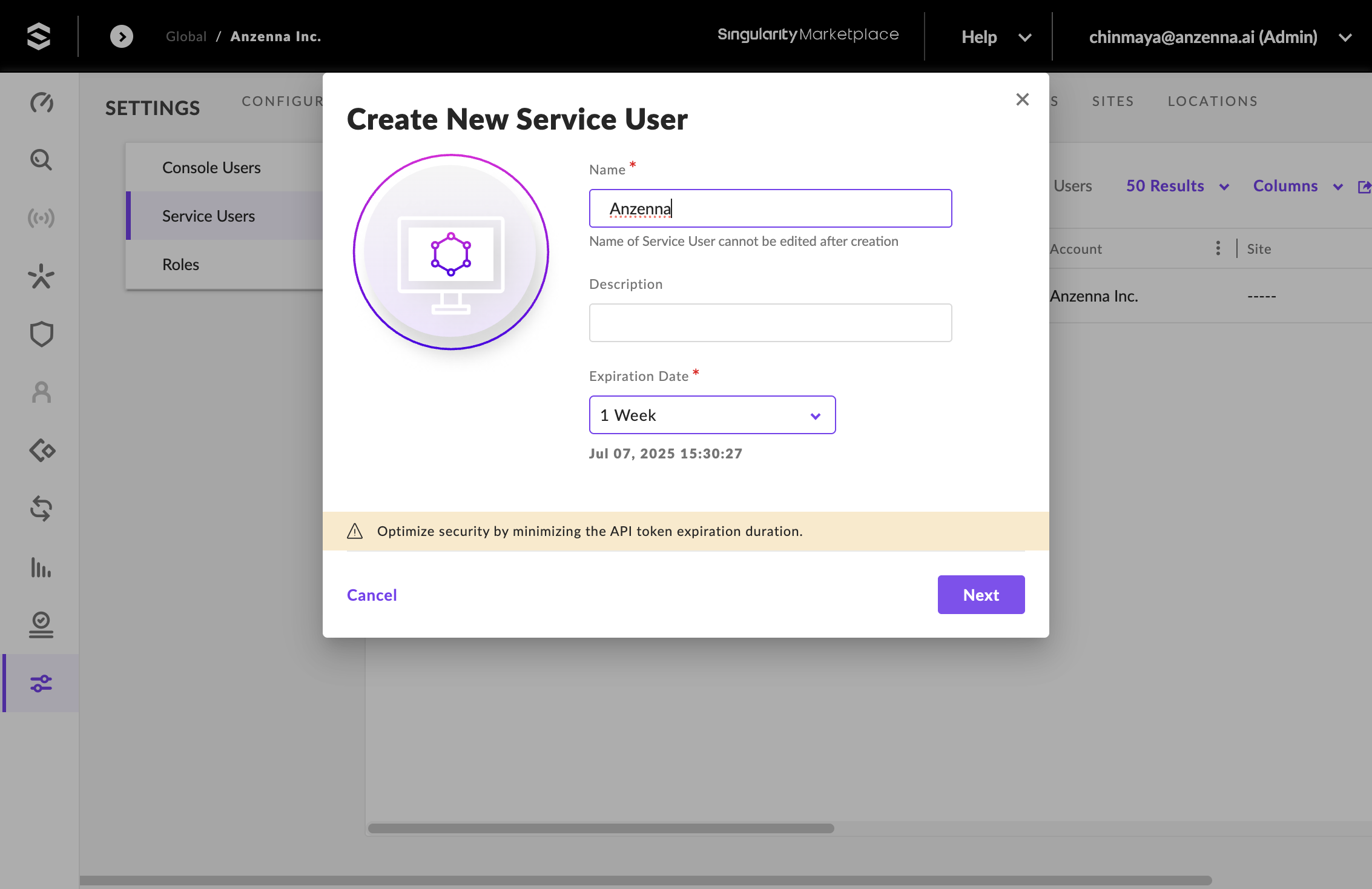
Navigate to your SentinelOne Management Console and click on Service Users.
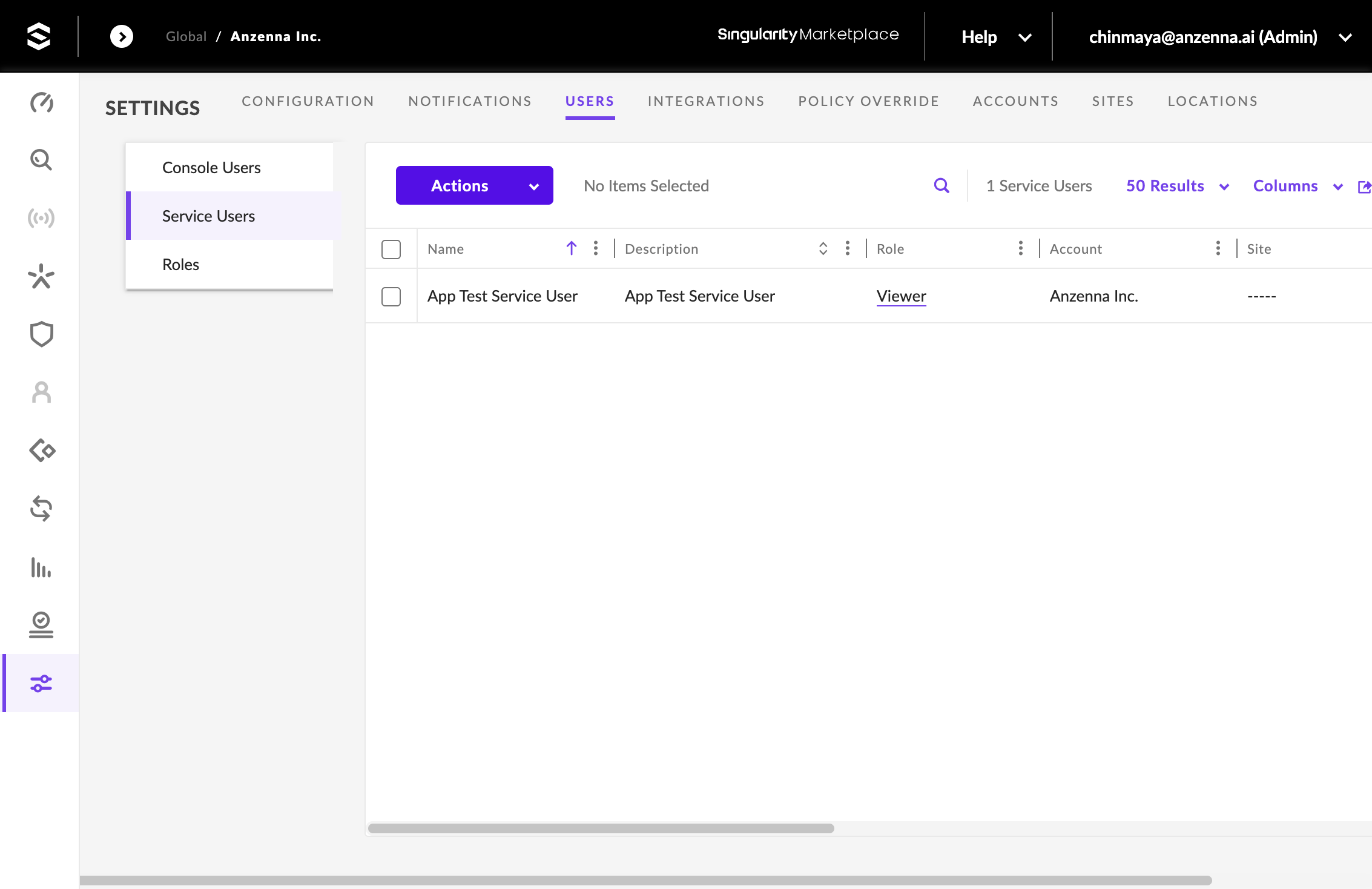
Click on Actions.
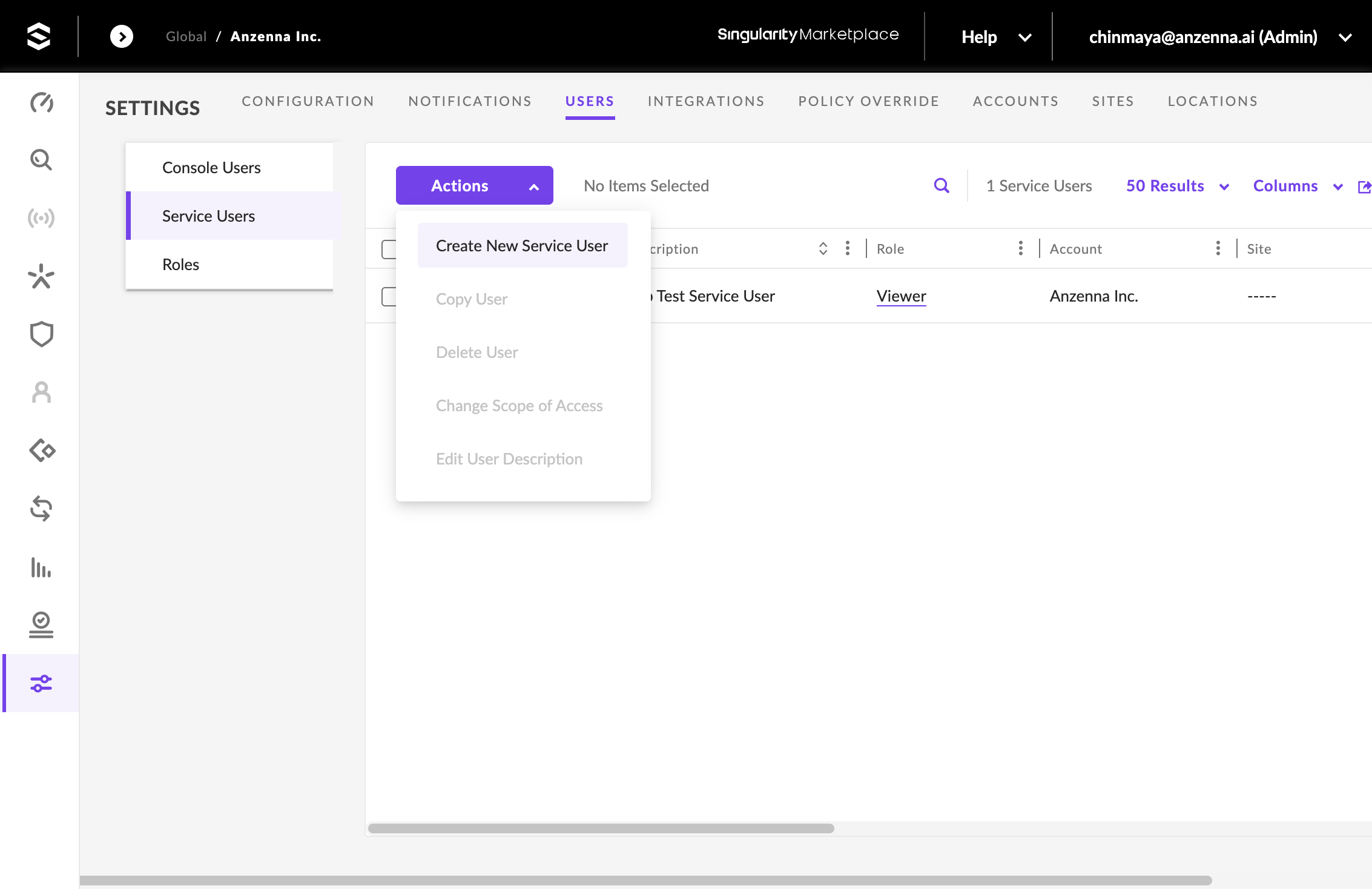
Click on Create New Service User.
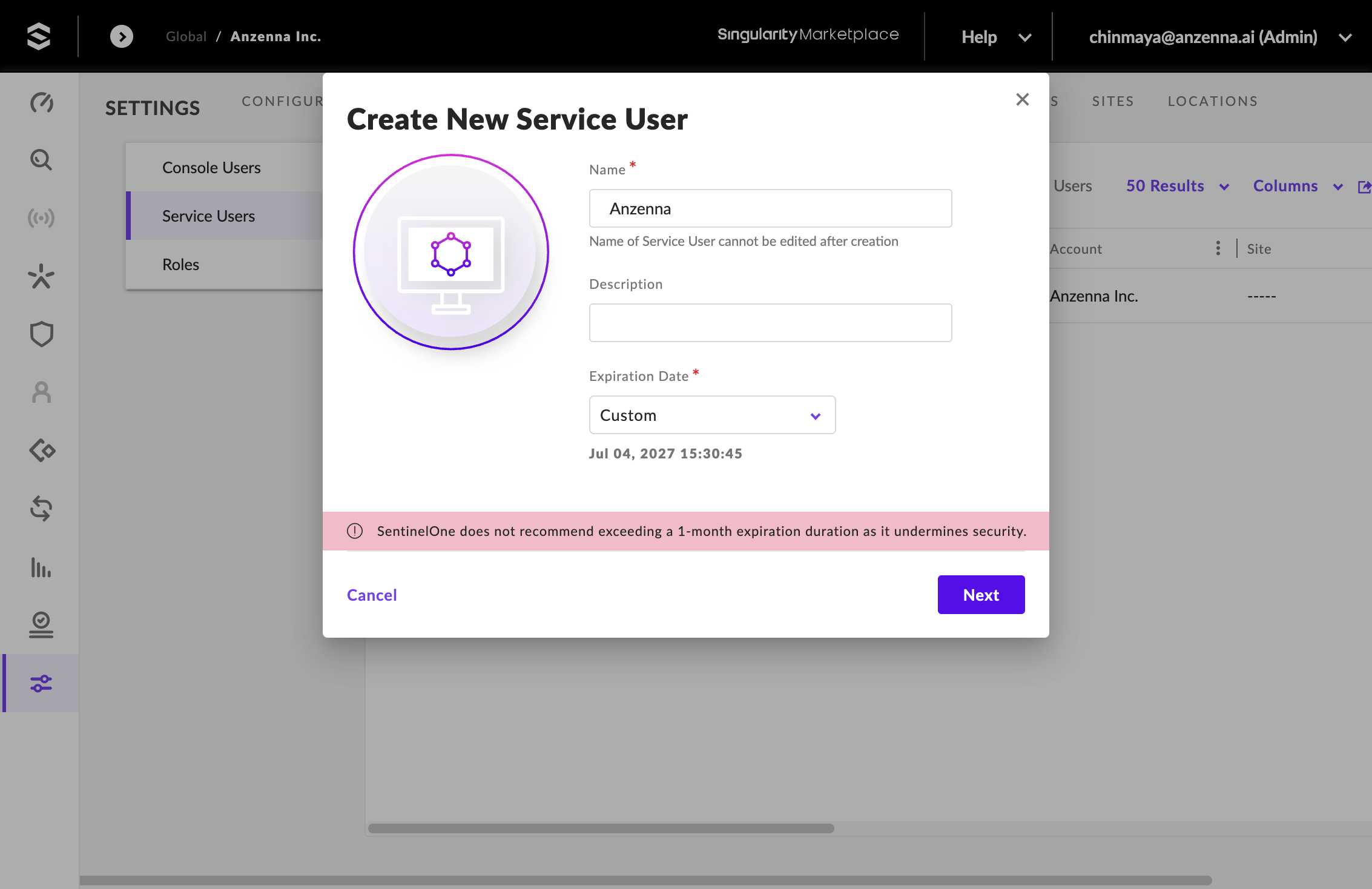
Type Anzenna as the service user name.
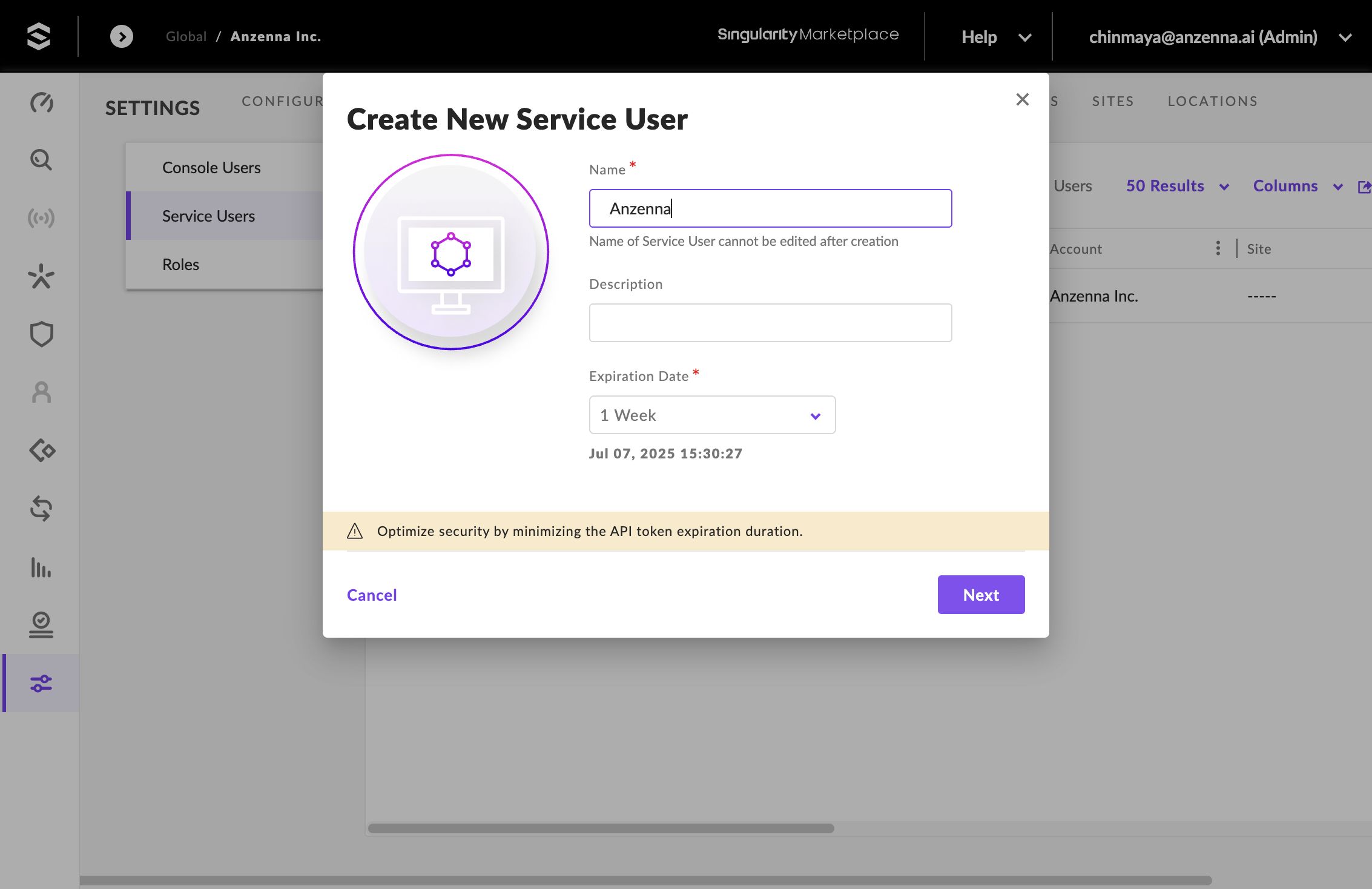
Part 2: Set Token Expiration
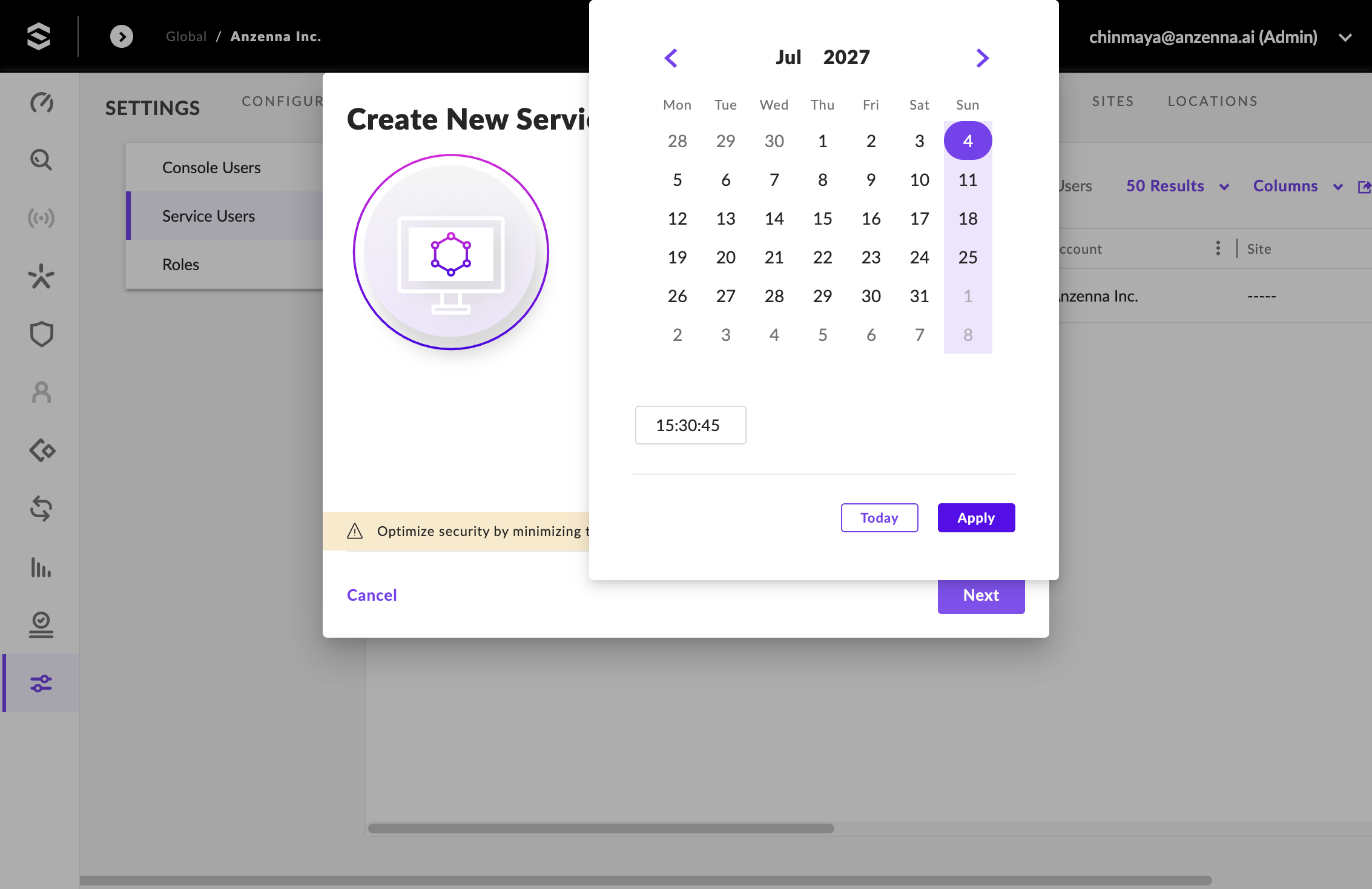
Click on the Expiration Date dropdown.
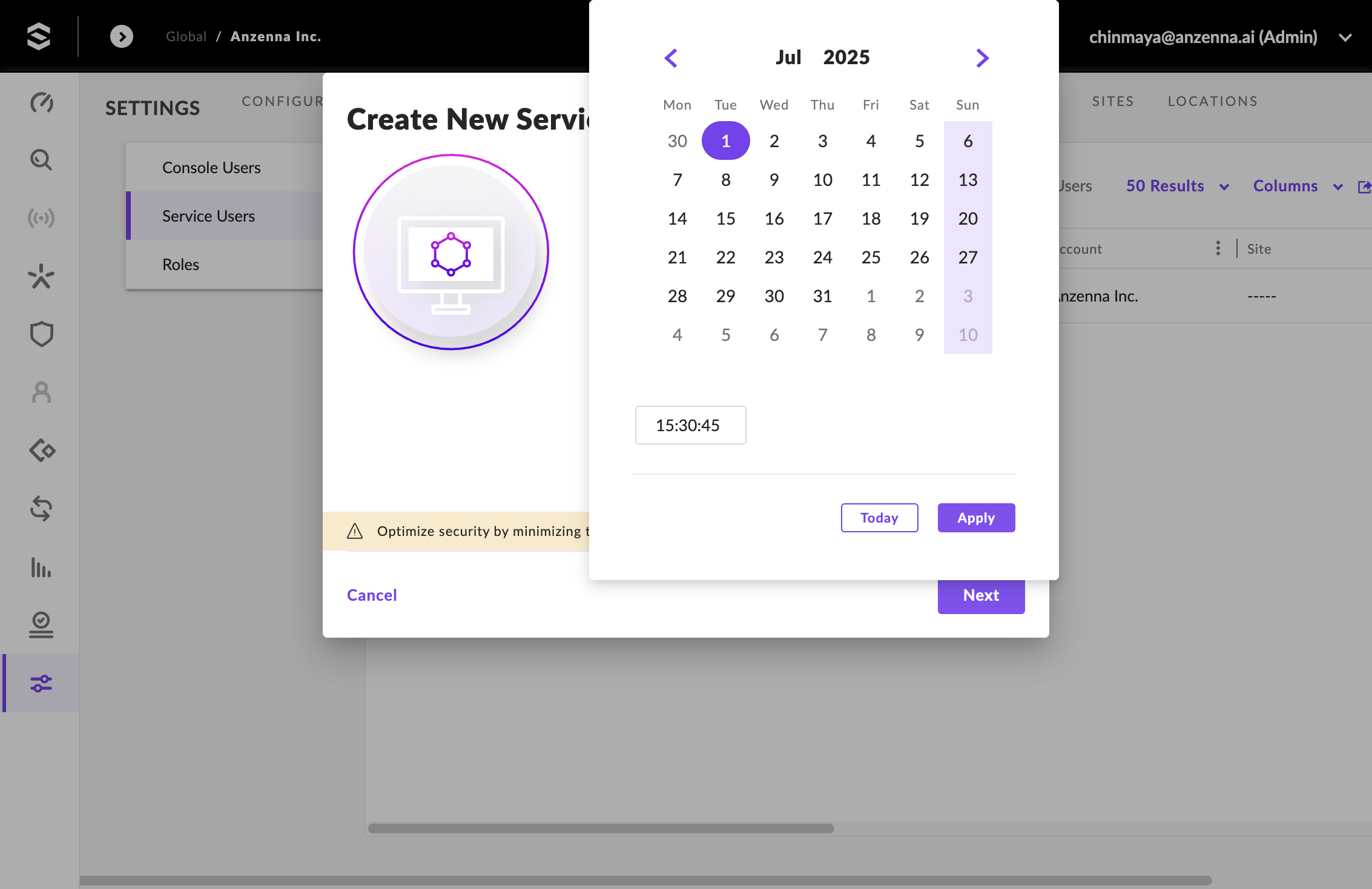
Click on Custom.
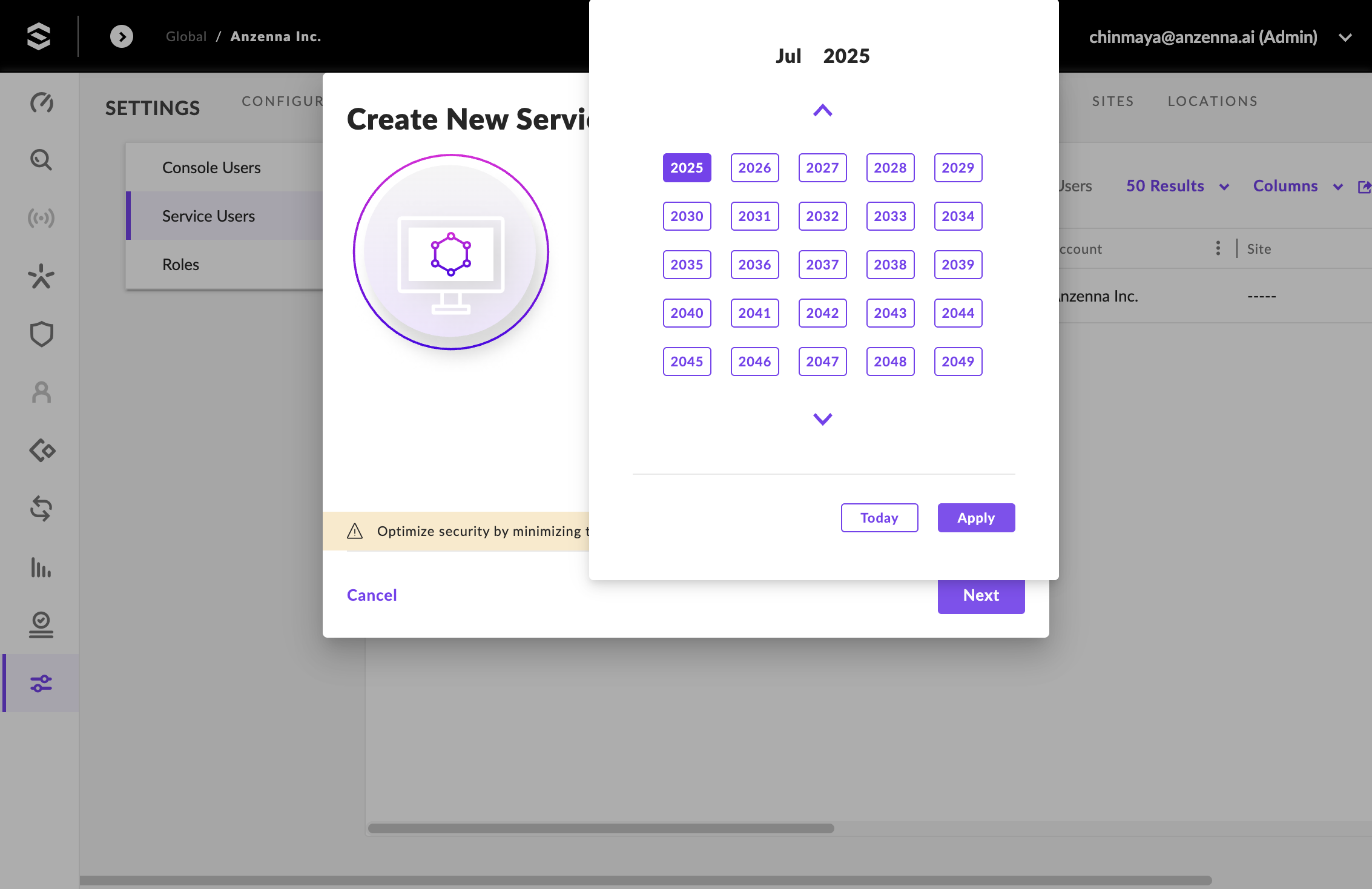
Pick a date, ideally 2 years out. Choosing a shorter time period will result in needing to rotate the API key sooner.
- Pick a year.
- Pick a specific date.
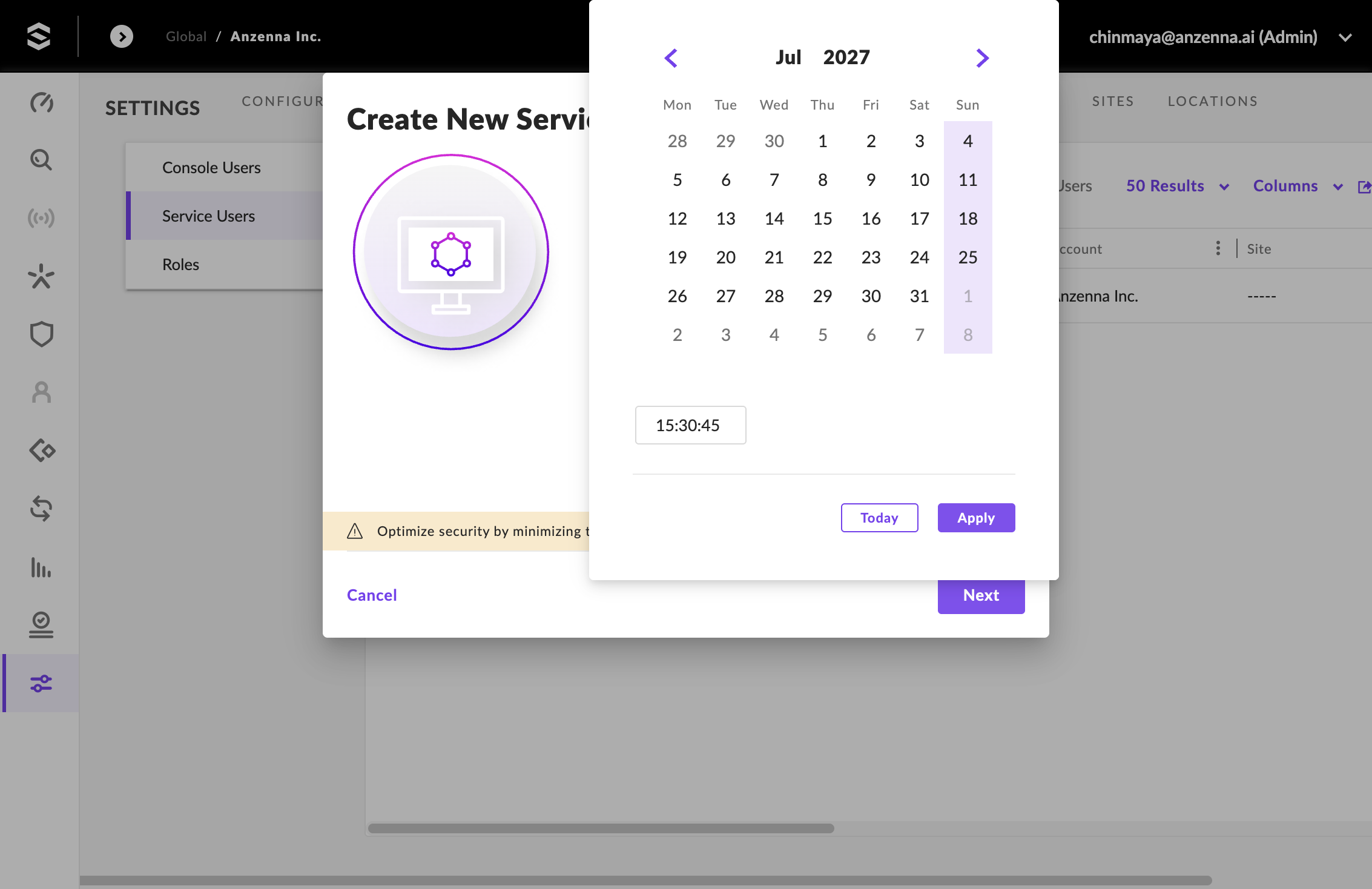
Click Apply to confirm the date selection.
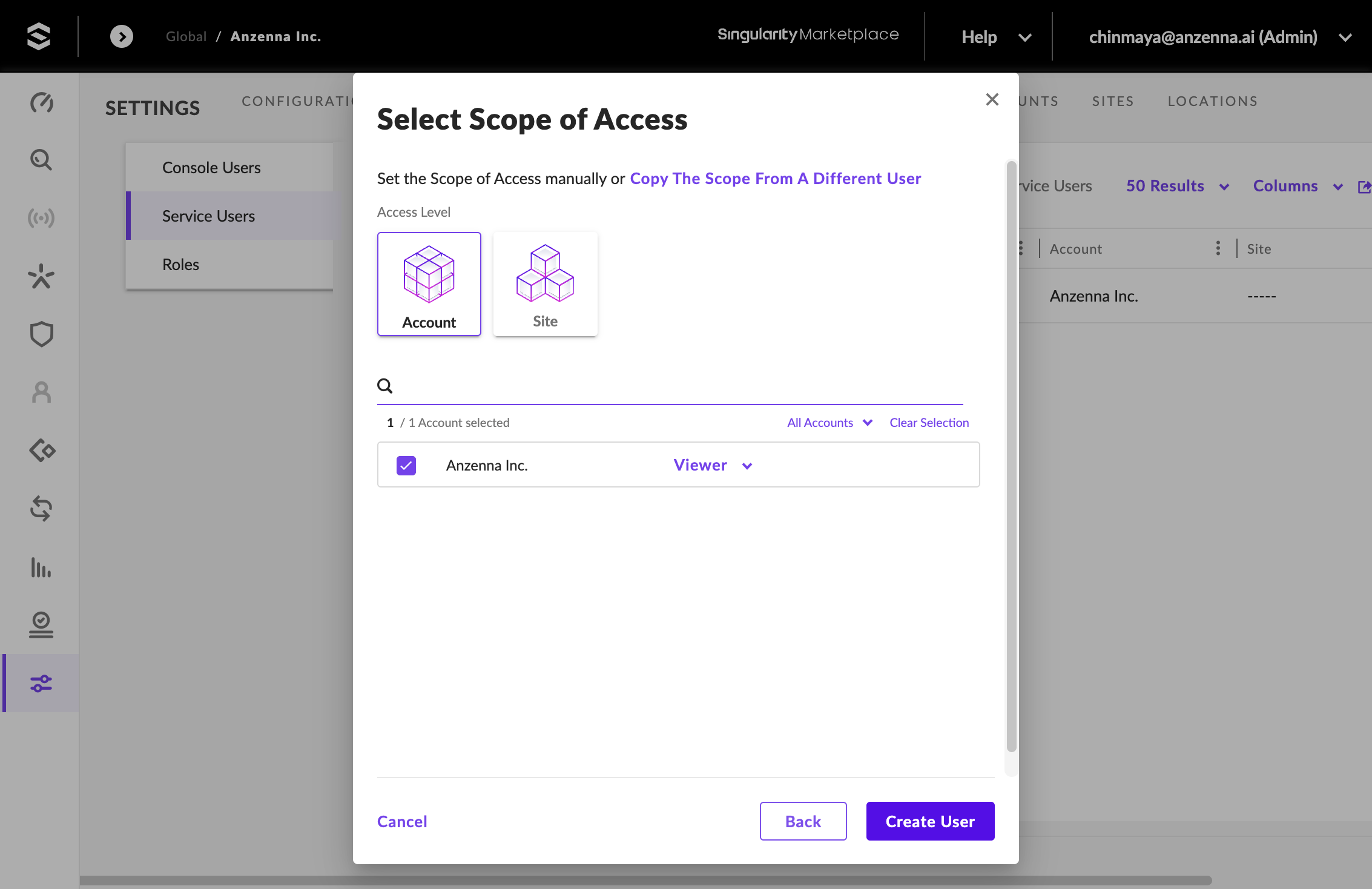
Part 3: Configure Scope and Create User
Click Next to proceed to the scope configuration.
Click on Select Scope of Access.

Select the appropriate scope of access for your organization.
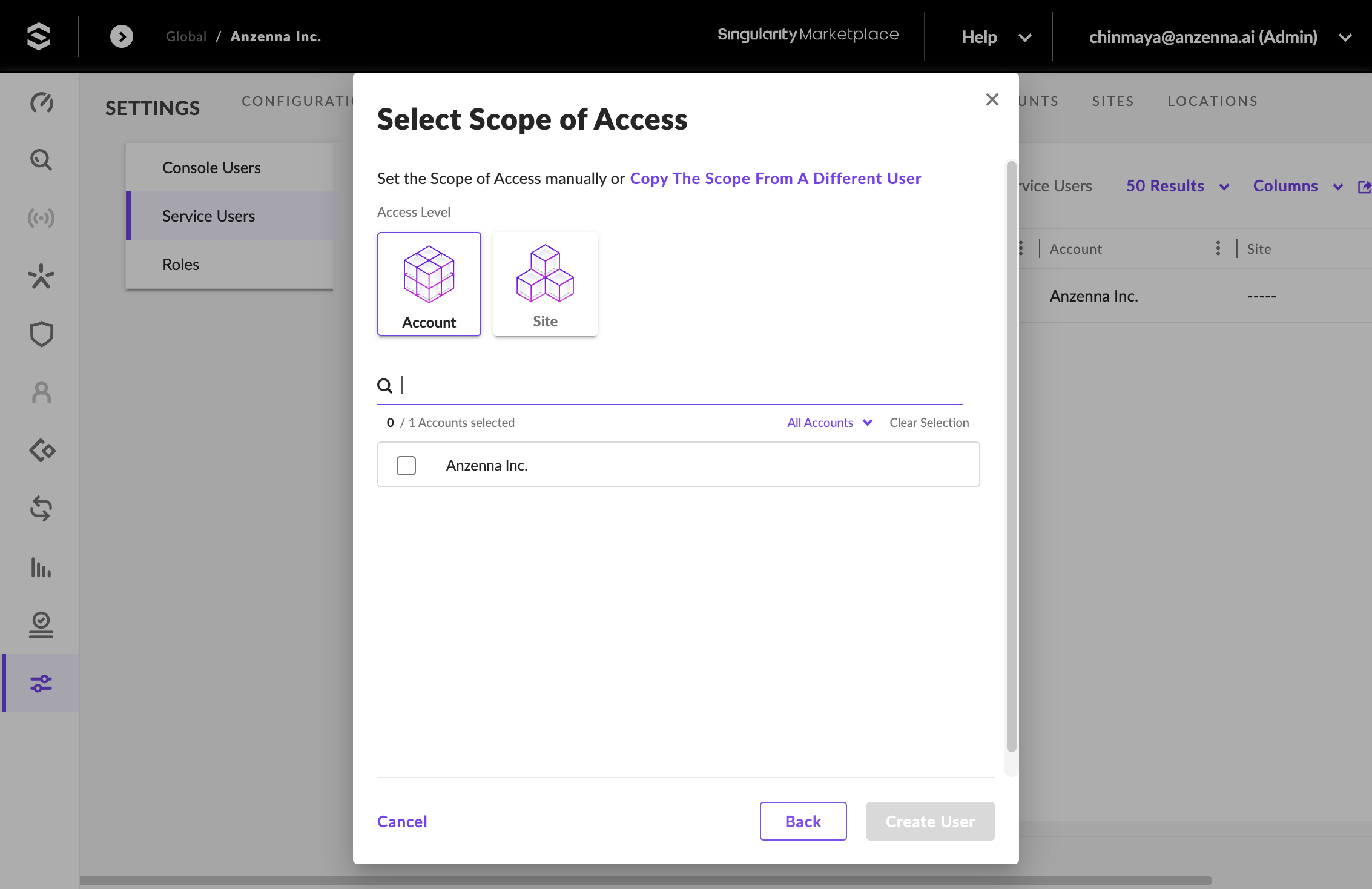
Click Create User to finalize the service user.
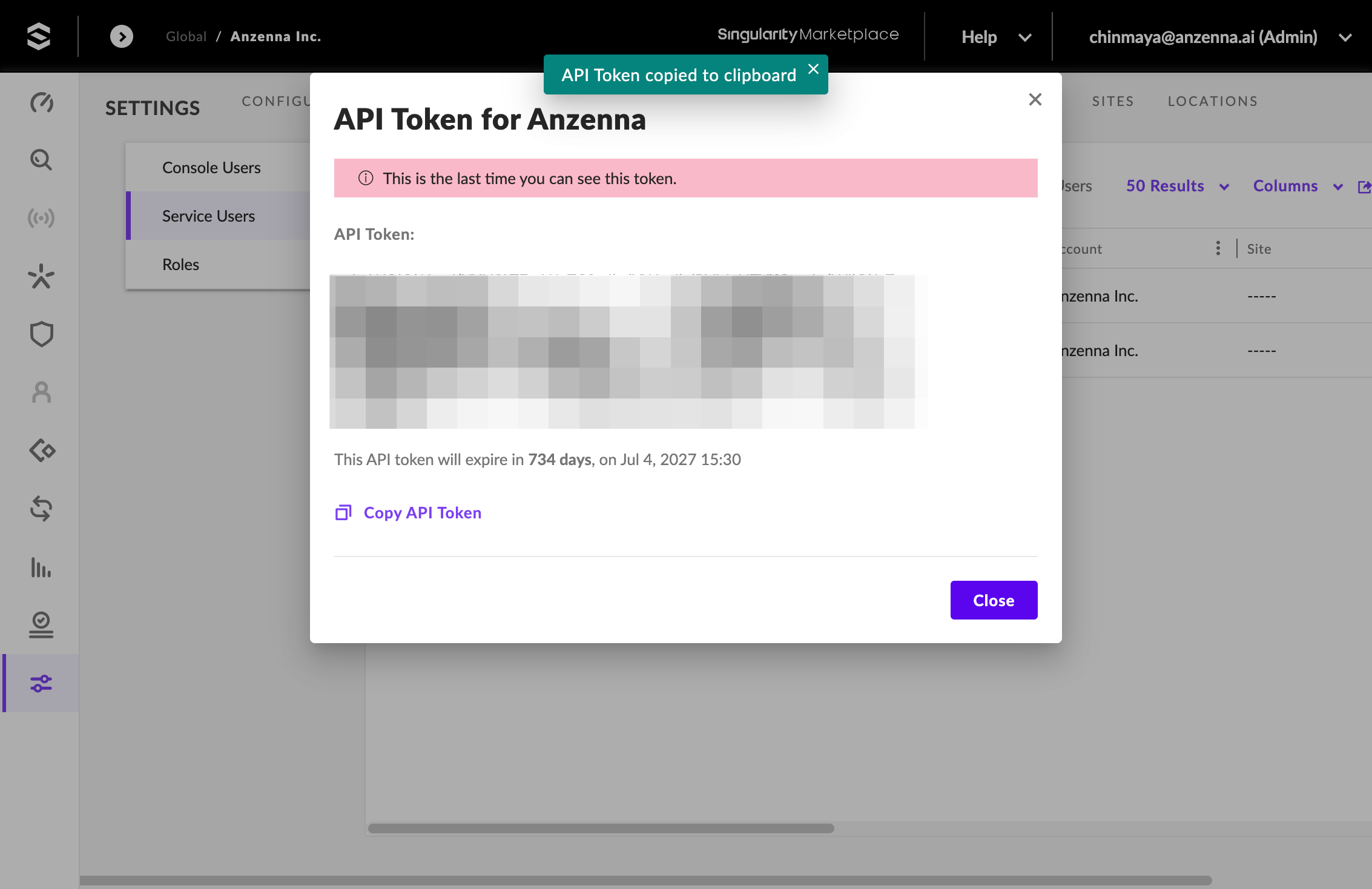
Part 4: Copy the API Token and Complete Setup
Click Copy API Token to copy the generated token.
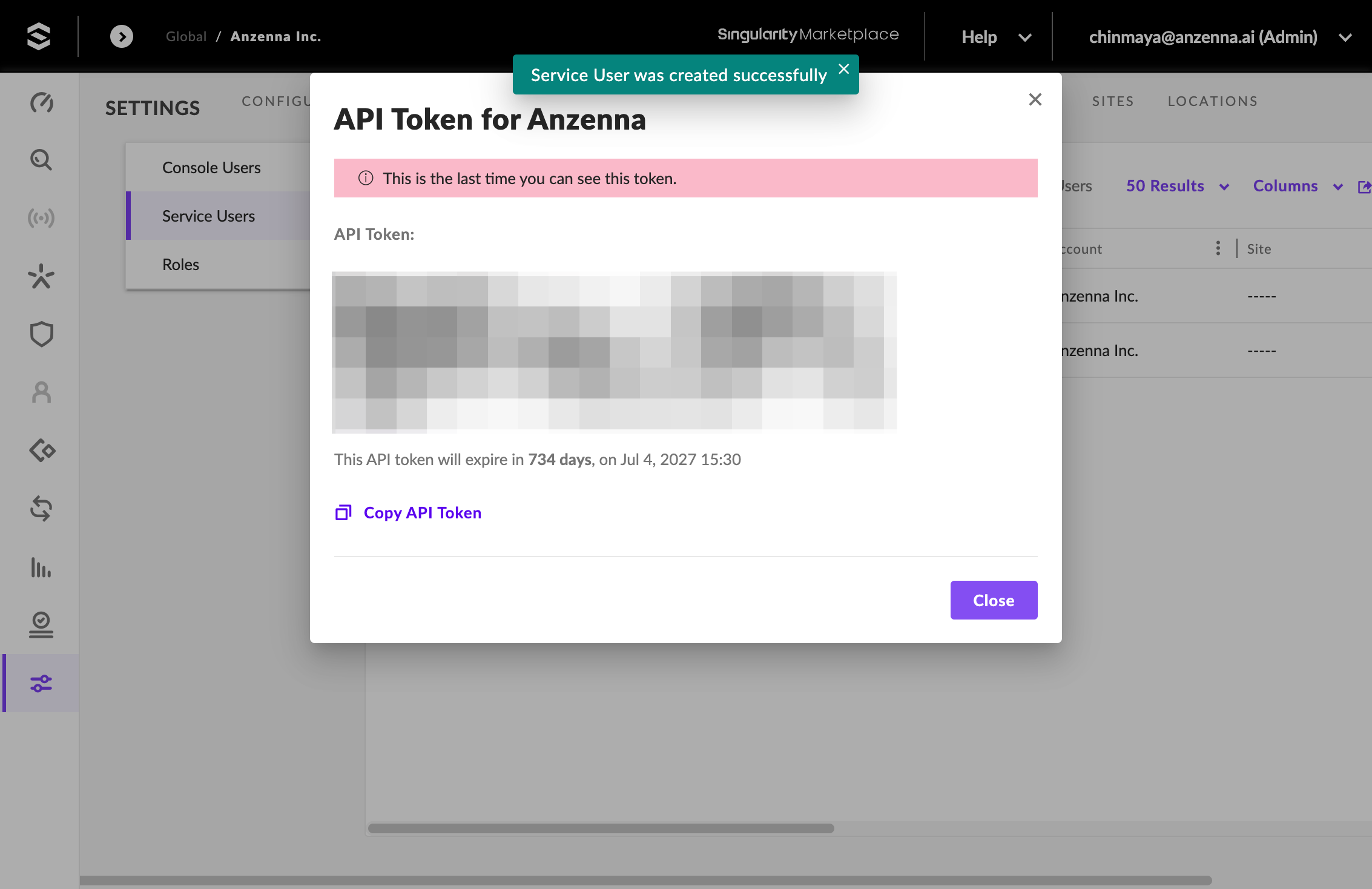
The API token is only shown once. Copy it immediately and store it securely — if lost, you will need to regenerate a new token.
Click Close to exit the dialog.
In Anzenna, navigate to Settings > Integrations, find the SentinelOne card, paste the API token, enter your SentinelOne console URL, and click Save.
Your SentinelOne integration is now active. Anzenna will begin collecting endpoint data for security monitoring and threat visibility.